Security threats that hinder people’s digital and financial security will create doubts in the minds of users. The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted. SecureDrop is a popular site where whistleblowers can anonymously share confidential information with journalists.
Is The Dark Web Illegal?
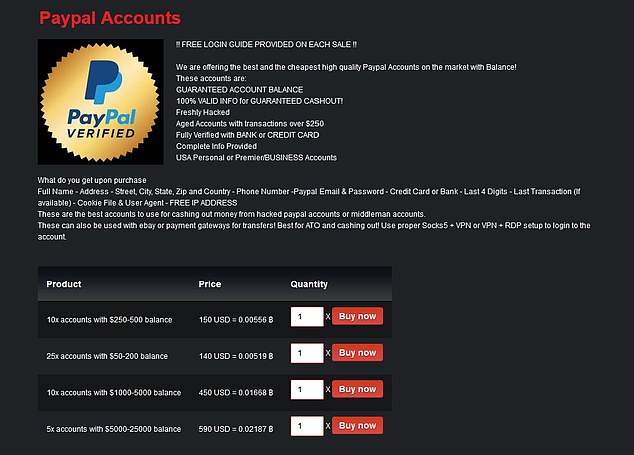
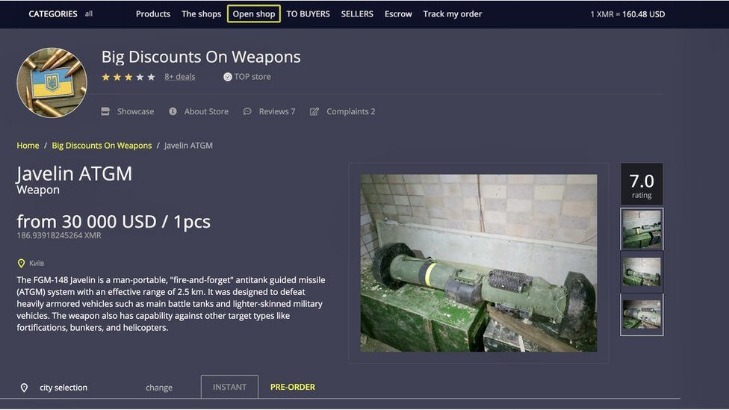
Thus, use the best antivirus software that protects against these online threats. The website allows visitors to view all the goods and services on display before they buy something. The quantity, price, and characteristics of the product are all provided. However, the platform lacks an advanced search option and a wallet-free payment option. To prevent the users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers. Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea about the vendors for the buyers and vice versa.
It aims to preserve the internet’s scientific and cultural heritage. ProtonMail is a Swiss-based email service that is very easy to use. You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. It is an excellent option if you want to surf the web anonymously.
BBC News (and Other Leading News Sites)

We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said.
Essential Tools For Finding Reliable onion Links
ProPublica has a reputation for unwavering investigative journalism. In 2021, they showed how tax rates benefit the rich, and they relied on stolen or leaked IRS documents to do so. In addition to the surface web, ProPublica also hosts their site on the dark web, because they want to make sure that everyone can access their reporting.
Share This Article
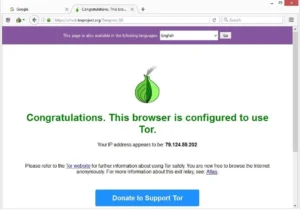
The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely. The following tips are for you if you are an enthusiastic Windows user and sick of switching to other operating systems. It is safer to tighten the seatbelt for protection, as a user of an unknown domain. Your operating system (whatever version of Windows) is supposed to be modified and running perfectly. Users should also have a dedicated alternative with an active firewall, although the Windows version would be appropriate.
Dark Web Sites Enabling File Sharing
He has worked for several international tech platforms, and his writing and editing expertise has also enhanced over time. He loves covering topics about VPNs, online privacy, and anonymity and shares his knowledge of online security with internet users through his words. Awazon Marketplace is the leading dark-web marketplace that claims to provide a secure destination for anonymous trading.
Should I Use Services Like Web2Tor?
If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year.

Safety Precautions When Accessing The Dark Web
Like any other crypto wallet, you can trade Bitcoin using Hidden Wallet. But unlike other wallets, you don’t have to worry about your personal information being leaked since it’s hosted on the Tor network. Hidden Wallet promises bank-grade security for your Bitcoins and claims that it can never access your keys or crypto funds. Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile.
How Do I Use A VPN With Tor?
- It will encrypt your traffic and data so no one can intercept it.
- It is safer to tighten the seatbelt for protection, as a user of an unknown domain.
- This commitment underlines the search engine’s dedication to providing a safe and constructive environment for dark web exploration.
- If you are a Linux user, then the easiest and fastest way to go is by Paws.
- All that one can expect from a deep web marketplace when it comes to anonymity and security.
Always run the latest version of the Tor Browser to protect against security vulnerabilities. Outdated versions may contain weaknesses that attackers can exploit to compromise your anonymity. I recommend enabling automatic updates and checking for new versions before each session.
It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading. Sections of the dark web are often closed down too, as part of police operations. Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions.
The service retains no copies of any data that passes through a ProtonMail account. Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail. The New York Times can also be anonymously accessed via the dark web.