Many users now leverage Tor to browse both the public Internet and the deeper parts of the...
access
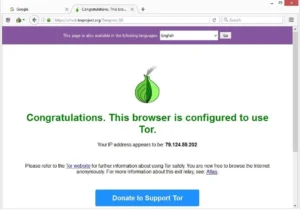
After installation, verify the file’s authenticity using PGP – the instructions are on Tor’s website. If you’re...
This deep web search engine can be accessed via the surface web and Tor. It filters out...
In other words, the deep web covers everything under the surface that’s still accessible with the right...
You might also consider using virtual machines (VMs) for an added layer of security. Tools like VirtualBox...
These computers are all owned by volunteers, passionate about privacy and happy to offer up their device...
You’ll also enjoy its Smart DNS support, 24/7 live chat service, the Keys password manager, and a...
Finally, many people consider the dark web a necessary tool for privacy and freedom of speech. In...
Surfing the Dark Web on an iPhone takes a few extra steps compared to Android. The official...
You should always use anonymous crypto wallets or stay away from dark webshops. Even if you’re already...