According to this keyword-based basic search with the stated false positive and false negative estimation, 18.5% of unique websites hosted through the Tor network share CSAM in December 2022. When a website has multiple alternate onion domains, we eliminate duplicates. As expected, the algorithm returns a smaller subset – 2142 domains that present unique websites. We investigate the years 2018–2023 and use a random sample of 10,000 unique onion domains for each year. Computer-generated random sampling guarantees the genuine randomness of our methods when we refer to random selection in this study.
Related Content
The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. Whether local or international goods, research documents, banned drugs, you name it, everything is available on this dark web platform (that’s one of the reasons why this should be monitored for security purposes). The site, described by officials as being “among the first of its kind to monetize” child porn using Bitcoin, was driven — and funded — by cryptocurrency.

He Helped Run One Of The Largest Child Porn Sites How Long Should He Serve In Prison?
According to new research collected by data analyst Semrush, Omegle grew globally from about 34 million visits a month in January 2020 to 65 million in January 2021. Despite the lack of physical contact, it is still considered abusive behavior for an adult to be engaging with a minor in this way. Adults may offer a young person affection and attention through their ‘friendship,’ but also buy them gifts both virtually and in real life. They look to try and isolate a child from their support network and create a dependency so that they establish a sense of power and control over the child. This can often feel confusing for a young person as it may feel as if this person truly cares about them.
What Parents Need To Know About The Darknet
Tech companies, law enforcement agencies and legislators in Washington responded, committing to new measures meant to rein in the scourge. While it is recognized that the darknet was initially used to create an application or modus for free speech, particularly in areas of political conflict, in reality, its anonymity has rendered much of the darknet a criminal marketplace. As per the Global Commission on Internet Governance (Global Commission on Internet Governance 2015), “the darknet certainly is the seedy underbelly of the Internet. Its sordid nature is exemplified in a few stories about drugs, assassination, trolling and child abuse” (p. 2). “In the past two months, we have seen an escalation in the type of content being shared on social media platforms, which became much more explicit than what we used to see in the past,” Paltieli told Ars. Shehan told Ars that “NCMEC has received at least a dozen CyberTipline reports submitted by companies regarding individuals attempting to upload known CSAM” into AI image generators to influence the kind of content that can be created.

Sky News Services
These individuals are motivated to seek help, but the help is largely currently unavailable. There is a growing global epidemic of CSAM usage, and some describe masturbation and pornography as coping mechanisms to alleviate economic strain, feelings of isolation, depression, and anxiety21. Such public health prevention programmes should be initiated, financed, evaluated, and developed not by a single industry or actor but as part of a holistic approach. It must be the task of a broad range of actors to take responsibility for the prevention of sexual violence against children, including but not limited to governments, the technology industry, international organisations, and civil society. We propose an intervention strategy based on our observation that some CSAM users do indeed recognise their problem.
The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. The survey does not request any personally identifiable information from respondents – such as age, country, or gender – that would put privacy at risk. Questions avoid specifics of criminal conduct (e.g., time, date, place, or victim details). We ask CSAM users about their thoughts, feelings, and actions related to their use of CSAM so that in the future we can build a cognitive behavioural theory-based anonymous rehabilitation programme for CSAM users. We demonstrate that not only are CSAM websites widely hosted through the Tor network, but that they are also actively sought.
This raises the question of the commonalities between CSAM use and addiction. Many users are not just passive observers of CSAM; rather, they are sexually motivated6. Previous research has suggested that problematic use of legal pornography can escalate to violent sexual behaviour and the use of CSAM. Consumers who view legal pornography and engage in masturbation fuel this process of escalation by providing themselves with a ‘powerful neurochemical reward’ through orgasm7. This process, along with repeated exposure, may condition users into continuing to use the material despite possibly wanting to stop6. But despite an increase in productivity and the availability of new tools and technology, the IWF’s humble resources remain overwhelmed by the sheer scale of the task it faces.
Protecting Your Child’s Digital World With Safes
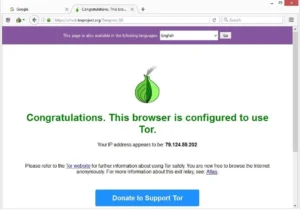
- Tor is an overlay network that exists “on top” of the internet and merges two technologies.
- Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
- Many young people view their digital self as an extension of their identity and sense of self.
- Questions avoid specifics of criminal conduct (e.g., time, date, place, or victim details).
- Despite its mandate by Congress, the center is not subject to public records laws and operates with little transparency.
However, even in the high profile case of Silk Road 1 being taken down by the FBI; within a month, the Silk Road 2 site popped up on its place. Interestingly, the Tor browser was originally invented in the 1970s by the United States Department of Defense (Advanced Research Projects Agency Network – ARPANET) so they could browse the net without being recognized. The same technology used for national security is the very software being utilized by users of the dark net, the criminals and those using it for social benefit. “What proportion are people and which are something else? We simply don’t know.” he said, adding that “crawlers” run by law enforcement and other agencies that police abuse sites could be responsible for the steady stream of traffic. The study found that the biggest number of hidden services were dedicated to selling illegal drugs. Also in the top five were underground markets, fraud sites, mail services and those dealing in the virtual currency Bitcoin.
Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. The rise of cryptocurrency and the dark web has created an anonymous, burgeoning, and borderless criminal marketplace, which governments around the world have at times struggled to tamp down on. The world’s “largest” dark web child porn site, which boasted “more than a million” downloads, was shuttered after international authorities said they followed a seedy trail of Bitcoin transactions. Finally, suggest screen-free activities that you can all do together during your downtime.

What Is Tails Software Used For?
The South-Korea based website, called Welcome To Video, relied on the bitcoin cryptocurrency to sell access to 250,000 videos of child sexual abuse, including young children being raped. “Without proper controls, generative AI tools provide a playground for online predators to realize their most perverse and sickening fantasies,” wrote IWF CEO Susie Hargreaves OBE. “Even now, the IWF is starting to see more of this type of material being shared and sold on commercial child sexual abuse websites on the internet.” Most traffic to sites hidden on the Tor network go to those dealing in images of child sexual abuse a study suggests.
Prosecutors said the site had offered videos of sex acts involving children, infants and toddlers – and specifically asked users not to upload videos featuring adults-only pornography. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing.
Children Engaging In Sex Acts
Since most cybercriminals and malicious individuals utilize the dark web to carry out illegal activities, it’s best to secure yourself with a VPN and antivirus software so that you can keep away from all the dangers of the dark web. Another website is Dread, which is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new markets, share onion links, add reviews, and much more. Unlike other search engines, it does not collect or share web activities and personal data of users. Studies suggest that the majority of Tor hidden service activity is illicit.
Best Dark Web Sites: Unseen Onion And Tor Links
The Dark Web isn’t a place for everyone but it’s worth exploring some parts of it. For those who may be a little faint of heart – we have listed 50 Legit Dark Web sites you can visit. The NCA said seven men have already been convicted in Britain since the first suspect was arrested in 2017. One man “was jailed for 22 years for raping a five-year-old boy and appearing on Welcome To Video sexually abusing a three-year-old girl.” “You are unable to live in civilized society without harming children,” she said, before ordering what amounts to a life sentence. McIntosh revealed some of those offenses voluntarily in interviews with investigators, Serafini said.
Since Verizon acquired the company in 2017, the spokeswoman said, its practice was not to alert users of police requests for data. Verizon recently sold Tumblr to the web development company Automattic. Multiple police investigations over the past few years have broken up enormous dark web forums, including one known as Child’s Play that was reported to have had over a million user accounts. “Some of those arrested not only uploaded and watched videos but also abused children,” Europol said, while confirming that “the investigation is ongoing,” making it appear likely that more arrests could follow. Arrests spanned the globe, including 16 in Spain, where one computer scientist was found with an “abundant” amount of CSAM and payment receipts, Todo Alicante reported.
Of The Best Dark Websites Google Won’t Let You Find
But not only did she not realize she was in peril, she was becoming more and more determined to demonstrate she could handle it. The monitoring of forums by outsiders can lead to actionable interventions, such as the successful profiling of active offenders. Some agencies have explored using undercover law enforcement officers, civil society, or NGO experts (such as from the WeProtect Global Alliance or ECPAT International) to promote self-regulation within these groups. The pedophile (eroticization of pre-pubescent children), hebephile (pubescent children) and ephebophile (adolescents) communities are among the early adopters of anonymous discussion forums on Tor.