The illicit activities of fraudsters are happening across the Gray, Deep, and Dark Web. But the real battle against fraudsters is on the Deep and Dark Web, where tracking their activity is much more difficult. Choosing the right Cyber Threat Intelligence platform can be the best weapon to win the war and protect your organization and customer data. Deploying a CTI solution will allow you to monitor and gather data on what’s happening on the Deep and Dark Web get alerts on activity specific to your organization. Fraudsters who have hacked into systems and stolen data oftentimes turn to the Dark Web to sell what they’ve gathered.
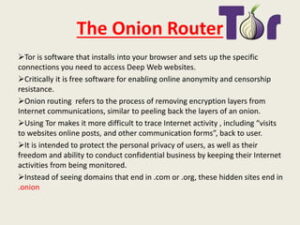
Tor encrypts your traffic through multiple relay nodes, but it’s important to understand that this encryption is removed at the exit node before reaching its final destination. This means that if you’re accessing non-HTTPS websites, the exit node operator could potentially view your unencrypted traffic. The deep web — also known as the deep net — is a collective term for non-indexed websites that are invisible to traditional search engines.

How To Access The Deep Web?
However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
As with all things business, the search engines are dealing with weightier concerns than whether you and I are able to find the best apple crisp recipe in the world. They want to help corporate powers find and use the deep Web in novel and valuable ways. Data in the Deep Web is hard for search engines to see, but unseen doesn’t equal unimportant. As you can see just from our newspaper example, there’s immense value in the information tucked away in the deep Web. All of those challenges, and a whole lot of others, make data much harder for search engines to find and index. Keep reading to see more about what separates the surface and deep Web.
- These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
- It provides an .onion URL and an interface for you to manage your Tor site easily.
- Access to these databases is typically gated by institutional affiliation or payment, ensuring that only qualified individuals can use them.
- The dark web, however, requires special software to access, as explained below.
- As cyber threats evolve, having visibility into hidden layers of the internet is no longer optional—it is strategic.
More Ways To Stay Safe On The Dark Web
Regrettably, it remains a considerably misunderstood realm, frequently conflated with the Dark Web, owing to inaccuracies in media coverage and distortions in portrayals on television and in film. Even government websites, health portals, and legal document repositories use the Deep Web. Systems like court records, tax filings, and digital medical histories all reside within protected databases designed to safeguard sensitive data. Without this hidden architecture, the internet would be a far more dangerous and chaotic space. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017.
The goal of TOR was to allow secure communication by intelligence sources in dangerous environments and has since been adopted by the general public for secure, anonymous browsing. The scale and impact of the Dark Web expanded with the development of cryptocurrencies like Bitcoin, which allow semi-anonymous financial transactions to be performed on the Internet. “The Dark Web” is an overused term that can be a source of mystery and confusion for most cybersecurity professionals.

Understanding BlackCat Ransomware: Threat Overview And Protective Measures
You can also find websites to download copyrighted material such as music, movies, games, software, and even Netflix credentials. Some downloads contain malware for the fraudsters to hack the unsuspecting user later. Law enforcement agencies don’t pay much attention to the Gray Web, so users don’t feel the need to be anonymous.
Surface web search engines do not index these sites, so you need the right tools to navigate safely and anonymously. The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines. Websites and pages in the deep web might include password-protected content, private forums, and personalized resources. The surface web, which is also called the visible web and the open web, is any website that search engines can add to their database.
Protect Yourself Against Tracking, Surveillance, And Censorship
You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live. The good news is that the BBC Onion site is an international edition.
Don’t Provide Personal Information
Sometimes, people also hide content from the surface web to protect copyright. For example, the Social Science Research Network has over 1 million academic papers uploaded. However, due to the intellectual nature of the papers, you need to create an account to access them. While operational, the Silk Road was the hub for various illegal transactions. Since the site ran on Tor, which granted a high level of anonymity, users could trade weapons, hard drugs, and other illegal substances.
Cyber attack services, like access to botnets that can conduct distributed denial-of-service attacks, are also available. The dark web contains content that’s only accessible through networks like Tor. Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous. The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki.
Regularly Update Security Software
The dark web, however, is a very concealed portion of the deep web that few will ever interact with or even see. In other words, the deep web covers everything under the surface that’s still accessible with the right software, including the dark web. If we continue to visualize the entire web like an iceberg, the open web would be the top portion that’s above the water. From a statistical standpoint, this collective of websites and data makes up under 5% of the total internet. That leaves U.S. law enforcement in the ironic position of attempting to track criminals who are using government-sponsored software to hide their trails.
However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. It allows you to search for images, maps, files, videos, social media posts, and more. You can choose the best darknet (.onion) website that suits you and start surfing.
Along those lines, we may consider as part of the deep web any website that asks for a login and password. In other words, many of the pages people access every day are actually part of the deep web. This includes social media profiles, email inboxes, and bank accounts. With the Deep Web, if you’re accessing personal accounts or sensitive data, the primary risks are related to security and privacy breaches.
Most internet users access the deep web almost every time they are online. For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. Some of these password-protected pages (deep web) are marked with a “no-index” tag which prevents search bots from crawling them. Others (dark web) use specific protocols that the normal browsers (Chrome, Edge, Firefox) can’t connect with.