“This is so fucked up man, we have the right to do whatever we want to our bodies.” A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange.
Deadpool / Vendor Stores
As major players tear each other apart, new, niche markets are carving out their own territories, often with a sharp focus on specific categories of illicit goods. Cybercriminals can rent or buy malware tools through darknet markets. This malware-as-a-service model allows less tech-savvy criminals to launch malware-driven cyberattacks without building the tools themselves. Most buyers and sellers use the Tor network, which hides IP addresses and locations. Doing so makes it harder for authorities to identify who’s behind a purchase or a listing. Vendors often build up reputations through ratings and reviews, just like sellers on mainstream platforms.

Community Forum / Arche Wiki / Patch Notes / Team
Another important source of information is the trading cash flow, which is recorded in the block chain and might contribute to a comprehensive view of the supply-demand relationship. We did not include such analyses due to the time and scope constraints, and it is a topic that we plan to investigate further. This finding is roughly in line with the observation of 57 opioid vendors’ origin in a marketplace named Cryptomarket during the period of October 2015 through April 2016, which was reported by Duxbury et al 6. In addition, we did not observe big changes in the top opioid commodity origins from 2014 to 2020. Particularly, as shown in Table 8, the United States and the United Kingdom are always in the top 5 advertised origins among years. We observed the same listings posted in different marketplaces and illustrate the dependency of the same opioid listings among different marketplaces.
Category Deep-dive: Illicit Drug Sales Grew And Expanded Outside Of Darknet Marketplaces In 2024
Ransomware actors and fraudsters are leveraging technological advancements, including cross-chain bridges and artificial intelligence, to bypass detection and scale their operations. Operation RapTor involves law enforcement actions taken by JCODE member agencies, including the DEA, FBI, FDA OCI, HSI, IRS-CI, and USPIS. State, local, and other federal agencies also contributed to Operation RapTor investigations through task force participation and regional partnerships, as well as the multi-agency Special Operations Division. McDonald recruited and hired accomplices to help package and ship the narcotics they sold on the darknet.

Fraud And Hacking Services
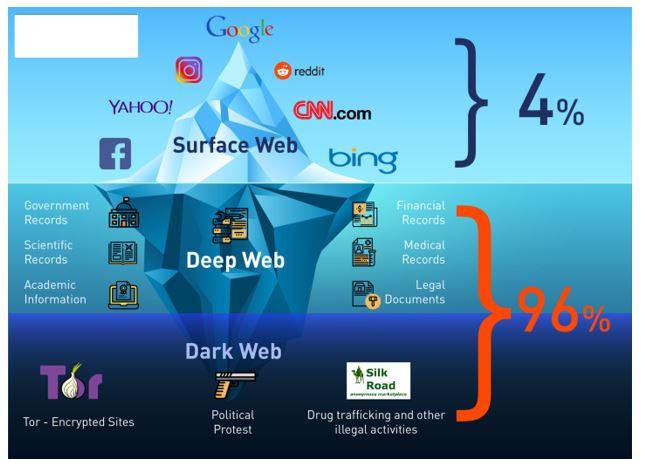
This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine. One option is to try DuckDuckGo’s .onion version, which is great for privacy.

For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live.
Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.
The arrest of Telegram’s founder, Pavel Durov, in August 2024 triggered a notable shift in the operational dynamics of the platform’s drug vendors. “Operation RapTor shows that the dark web is not beyond the reach of law enforcement,” said Head of Europol’s European Cybercrime Centre, Edvardas Šileris. “Through close cooperation and intelligence sharing, officers across three continents identified and arrested suspects, sending a clear message to those who think they can hide in the shadows. Europol will continue working with our partners to make the internet safer for everyone.” With so much money floating around these sites — dealers can make good money without leaving home — some vendors try to game the review system. Common tricks include creating fake accounts from which to post positive feedback; writing bad reviews of competitors; and even paying others to give favourable write-ups.
C The Tor Network
The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data.
Torzon Market
Trade is booming despite disruptions from law enforcement and particularly “exit scams”, in which market admins abruptly close down sites and take all available funds. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet.
- Darknet magazines and forums provide updates on new markets, onion addresses, and URLs, facilitating seamless transactions.
- OFAC’s designation of Parsarad was the result of strong partnership and coordination with the FBI, the Drug Enforcement Administration, Internal Revenue Service-Criminal Investigation, FinCEN, and a range of European law enforcement partners.
- Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity.
- These currencies enable seamless cross-border transactions without the need for intermediaries, reducing costs and increasing efficiency.
- According to court documents and statements made in court, Srinivasan and Ta used the “redlightlabs” darknet account to advertise and sell counterfeit M30 oxycodone pills containing fentanyl and other illicit drugs.
- Keybase also offers extremely user-friendly secure chat and file-sharing services through its app.
- Law enforcement authorities across Europe have dismantled Archetyp Market, the most enduring dark web drug market, following a large-scale operation involving six countries, supported by Europol and Eurojust.
- This includes using an anonymous browser like Tor, a VPN to encrypt your connection, an antivirus for protection against malware (we recommend TotalAV), and generally being careful not to reveal personal information.
- Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content.
- Taken together, those operations represent the most far-reaching collection of law enforcement actions against the dark web’s economy in at least two years.
Since the takedown of Nemesis, Parsarad has discussed setting up a new darknet marketplace to take the place of Nemesis with vendors that were once active on the marketplace. These markets have also improved their user interfaces, making navigation and product discovery more intuitive. The use of Tor and other privacy-focused tools ensures that users can access these platforms without compromising their anonymity. As the darknet ecosystem evolves, it continues to adapt to user needs, offering a reliable and secure environment for trade. Darknet market lists play a crucial role in simplifying access to these platforms. By aggregating verified links and providing up-to-date information, these lists reduce the time users spend searching for reliable markets.
Acronis Cyber Protect Cloud: New Version C2505
Asking the “right way,” according to Barratt, should yield enough information about the source of the substance to understand what type of risk it poses to the community if it turns out to be adulterated. This includes asking participants who say that their drugs are from “the internet” to provide more detail, if they feel comfortable doing so. Gibbons rejects the idea that shutdowns are a pointless and expensive waste of police time. “Although new DNMs have emerged, our work impacts on the trustworthiness of those running the sites. The replacement sites often take a considerable time to build up to the same vendor-customer base,” he said.
Some now offer customer support, escrow systems to prevent fraud, and even user-friendly interfaces that make illegal trade feel strangely routine. Still, the dangers are severe — exposure to scams, malware, surveillance, and prosecution are just the beginning. In this article, we’ll explore what dark web markets are, how they work, and why they’re so risky. We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there.
It publishes a newsletter in multiple languages and not only runs onion services for its website but all its email and chat services. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results. This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines. When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website.