Volunteers compile the list of links by hand, thus creating a high-quality index of deep web content across dozens of categories. It has copies of more than 850 billion web pages on its servers, allowing you to search for content that’s no longer available on the visible web. There is no official data available, but most experts agree that the invisible web is several times larger than the visible web.
And it can be dangerous if you slip up and your identity is discovered. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game. The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not. Services like Random Chat connects you with random people using the same service.
Navigating Ransomware Attacks While Proactively Managing Cyber Risks
Another standout feature is that the servers can’t see what you type, copy, paste, or send. To increase the security level, add password protection and determine the expiration time for messages. Hence, even if you hide your IP address, you aren’t completely secure. For all these reasons, at PrivacyRadar, we strongly discourage using Awazon or any other dark web marketplaces. It’s for the good that these sites are not available for the general internet user. It is important to note that the people or journalists who use ProPublica to spread their truth recognize the risk of doing so.

Indeed, we follow strict guidelines that ensure our editorial content is never influenced by advertisers. We always recommend using a reliable VPN when accessing the deep web or dark web. That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened.
- Law enforcement officials can exploit that weakness using “Tor-exit-node” monitoring techniques to expose users’ IP addresses and potentially trace activity back to the original users.
- For safer browsing, it is highly recommended to also use a VPN and antivirus software.
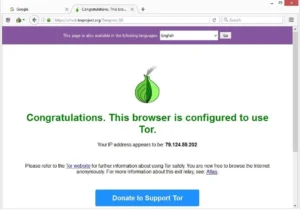
- The Tor Browser is the most popular browser for the dark web, but other popular options exist, like Brave, Comodo Dragon, Epic and SRWare Iron.
- RiseUp is a top dark web website that offers secure email services and a chat option.
This browser is a service originally developed in the latter part of the 1990s by the United States Naval Research Laboratory. All commonly public-facing websites accessed via traditional browsers like Google Chrome, Internet Explorer, and Firefox are contained here. Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search.
Never Share Personal Information
Users of the dark web should also realize that although their activity is technically anonymous, associating with people who are conducting illegal activities can have legal implications. One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity. This essentially means that over 93% of Tor daily users use the dark web for legitimate reasons.
What Should I Do If My Social Security Number Is On The Dark Web?
- It also includes a dark web monitoring feature that crawls the dark web and alerts you if your details show up anywhere.
- You can also find websites to download copyrighted material such as music, movies, games, software, and even Netflix credentials.
- Husain is also a part of the vpnMentor Cybersecurity News bulletin and loves covering the latest events in cyberspace and data privacy.
- Unlike the regular internet, the dark web doesn’t use standard URLs or search engines.
However, we do not advise readers to log onto this dark web mirror site; doing so would risk their privacy and that of others. However, there’s no guarantee that all the links on this site are working. Some may lead to malicious sites, downloading malware on your device. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous.
How To Stay Safe On The Dark Web
You don’t want to wake up one morning to find that the credit card details you stored on a Fintech company’s website are now on the first page of Google. From this, you can deduce that privacy and security are two of the greatest reasons for having content on the deep web rather than on the surface web. Earlier, we explained that the deep web is 400 times bigger than the surface web, but most people may not understand how big that is.
Dark web encryption allows website owners and users to stay completely anonymous during their engagement. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. Blockchain even has an HTTPS security certificate for even better protection.
Other Ways To Access Dark Web Platforms
On Tor, you can type in any URL you’d like to visit, including .onion links on the dark web. To discover content on the web, search engines use web crawlers that follow hyperlinks through known protocol virtual port numbers. This technique is ideal for discovering content on the surface web but is often ineffective at finding deep web content. I personally recommend Tor over VPN because it’s the safer option — the VPN encrypts your traffic and changes your IP address, so the Tor network can’t see them.
Tor Metrics
Traders cash in on stolen credit card data dumps, initial access points to vulnerable systems, credentials, and intellectual property belonging to companies compromised during cyberattacks. The dark web, however, requires special software to access, as explained below. Our editors thoroughly review and fact-check every article to ensure that our content meets the highest standards. If we have made an error or published misleading information, we will correct or clarify the article.
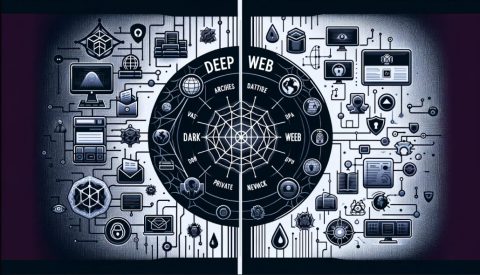
Businesses benefit from this, ensuring proprietary information remains exclusive. By volume, the deep web constitutes approximately 90% of all internet content (according to Google’s documentation mentioned above). Discover the key differences between the Dark Web and Deep Web, their uses and risks to businesses. David is a programmer and writer who has worked as a software developer at MIT.

These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. I2P can only be used to access hidden sites that are only available on the I2P network.
Legal Activities
Such data includes medical records, financial information, research papers, private forums and networks, and other content. This anonymity can be achieved in various ways, but most of the sites on the dark web are “onion” sites. They can only be accessed using Tor Browser, which gives users access to the Tor network.
The Best Dark Web Links — Safe & Verified Sites In 2025
The developers of ProtonMail recommend using the Tor browser to visit the dark web version of the service. This ensures greater security and privacy, making it much more difficult for snoopers to get in. In addition, you can connect your Keybase account with X, GitHub, or Reddit to let people easily trust that they are talking to the actual person. Also, the platform has a feature of automatic deletion of messages – set a timer and they will be deleted after a set period. Onion.name is a dark web resource that helps make sense of the mess of letters and symbols that usually form the darknet sites.