Researchers tracking these groups noted that Telegram’s broadcast and bot features allowed operators to recreate the functionality of darknet forums almost overnight. Law enforcement in Russia and Germany confirmed that Hydra affiliates were using Telegram bots to automate sales, effectively replicating market infrastructure in a mobile app. The way darknet actors coordinate has undergone a dramatic shift in the past decade. Once dominated by cloistered IRC channels and hidden .onion forums, the conversation has now moved to mainstream messaging platforms. Today, Telegram channels, bot networks, and private groups have become the default infrastructure for criminal coordination. This shift has not only reshaped how operations are run but also how law enforcement approaches surveillance and takedowns.
This fusion of AI with illicit marketplaces could open the door to new forms of large-scale fraud, intensifying the cat-and-mouse game between cybercriminals and law enforcement. Nexus Market emphasizes user-friendly navigation and community-driven content, offering detailed categories such as digital goods, personal data, and hacking services. It encourages vendor competition through frequent promotions and loyalty programs, making prices relatively competitive. Nexus also supports multi-signature escrow transactions, appealing to security-conscious buyers and sellers. WeTheNorth, launched in Canada in 2021, caters to both domestic and international audiences. It offers counterfeit documents, financial fraud tools, hacking services, and an active forum for community discussions.
Can You Find Leaked Credentials On The Dark Web?
In mid-2024, Telegram confirmed cooperation with European authorities to remove clusters linked to ransomware extortion leaks. While takedowns rarely eliminate operations, they force constant churn and reduce the longevity of large-scale hubs. For defenders, monitoring communication platforms has become as important as tracking marketplaces themselves.

Many of these big markets are now engaged in cyber warfare, with vendors and operators attacking each other to assert dominance, often leading to disruptions and shutdowns. This “market cannibalization” has further destabilized the landscape, pushing vendors and buyers to seek refuge in smaller, more secure spaces. If your personal data ends up for sale on the dark web, it can lead to serious consequences like identity theft, financial fraud, or unauthorized access to your online accounts.
Depending on jurisdiction, charges can range from possession of illegal substances to conspiracy and money laundering. Law enforcement increasingly focuses on large-quantity purchasers and those seeking especially dangerous products, such as firearms or specialized hacking tools. Even smaller transactions can trigger investigations, given the international coordination among agencies targeting the dark web. Consequently, anyone participating in these markets faces the dual risk of financial and legal jeopardy. MGM GRAND Market is a newer entrant distinguished by its focus on luxury-branded counterfeit items and high-stakes financial fraud.
In Review: Hacking Forums And Dark Web Marketplaces
The Russian Market has been around since 2019 and is one of the more prominent dark web marketplaces. Unlike many other dark web markets, Cypher does not require buyers to deposit cryptocurrency upfront, which reduces the risk of exit scams. It allows vendors to sell without registration, which provides an added layer of anonymity, making it one of the more flexible and user-friendly markets on the dark web. Bitcoin remains the most widely recognized, though it has become easier to trace through blockchain analytics. As a result, privacy-focused coins like Monero and Litecoin have gained traction among those seeking tighter anonymity.
For around $2, these items are designed to not only give scammers to those particular accounts but also get enough of a foothold into your personal data to commit identity theft. Once a hacker has pieced together enough of your personal info, they can open lines of credit in your name and cause you major problems that can be life-altering and very time-consuming to resolve. Remote Access Trojans (RATs) are one of the most commonly used hacking tools in the shadow market. With the increasing number of cyber intrusions, RATs have become a popular choice for hackers due to their ability to allow remote access to a victim’s computer system.
Scammers are targeting people via links to fake Manx Telecom bills using the firm’s email platform. User comments are still being posted on the marketplace’s news page, but in small numbers. The UK’s National Crime Agency insists that the operation has dealt a “huge blow” to cyber-criminals.
Is There Any Way To Automate Dark Web Monitoring?
A botnet is a network of compromised devices that attackers use for distributed denial-of-service (DDoS) attacks, overwhelming business websites with fake traffic. DDoS-for-hire services are available on the dark web for as little as $20 per attack. SAN FRANCISCO – The Justice Department announced today the seizure of Hydra Market (Hydra), the world’s largest and longest-running darknet market. In 2021, Hydra accounted for an estimated 80% of all darknet market-related cryptocurrency transactions, and since 2015, the marketplace has received approximately $5.2 billion in cryptocurrency. Encrypted communication channels on the dark web allow users to message back and forth in an anonymous online environment. However, some surface web platforms like ProtonMail offer encrypted email services in addition to dark web versions that enable people residing in more repressive areas to communicate freely.
Cryptocurrency
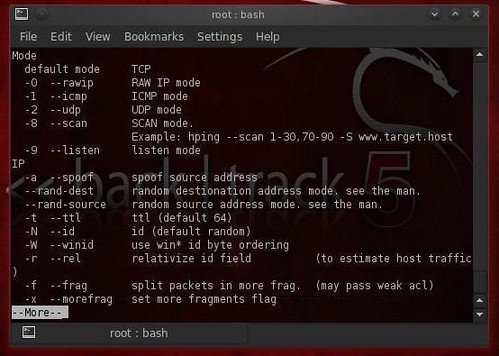
Beyond these specialized networks, users often connect through VPN services and proxy chains to further mask their physical locations. Ransomware groups increasingly leverage Darknet forums to recruit affiliates, trade exploits, and launder stolen funds. Cryptocurrencies serve as the backbone of these operations, allowing attackers to collect ransoms without tying payments to specific financial institutions.
Ethical And Legal Boundaries In Monitoring Darknet Marketplaces
- Where one marketplace collapses, Telegram facilitates dozens of replacements, each with lower visibility and faster growth curves.
- Yes, platforms like DeHashed, LeakLooker, and DeepPaste provide access to data breaches and leaked credentials.
- Despite increased law enforcement efforts and frequent marketplace shutdowns, darknet platforms continue to evolve, adapting their strategies to evade detection and maintain lucrative revenue streams.
- Phishing is a type of social engineering, which is a generic term used to describe attempts to manipulate or trick computer users.
Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities. The significance here lies in the potential damage to individuals and businesses. Companies must implement strong data security measures, employ encryption, and monitor for data breaches to protect customer and employee information.

Case Study: Genesis Market And Telegram Broker Networks
They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation. As darknets and dark markets continue to evolve, understanding their dynamics and implications is crucial for fortifying the cybersecurity defenses of individuals, organizations, and nations in the digital age. Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data.
Is It Illegal To Access The Dark Web?
It has a bidding feature, with new batches of stolen data being frequently added. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. See how our intelligent, autonomous cybersecurity platform harnesses the power of data and AI to protect your organization now and into the future. Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data.
- By implementing the countermeasures discussed in this section, you can reduce the risk of cyber threats and protect your digital security.
- One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S.
- An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions.
- Finally, as with most online accounts, fraudsters bank on the fact that many people still reuse passwords across multiple accounts, especially those they use often like Facebook.
- Stolen credit and debit card data, along with bank and online payment account details, have long been the most popular items for sale on the darknet markets.
RDP With Server Access

Social media platforms like Facebook and news sites like the BBC and ProPublica have also waded into the dark web’s waters. These legitimate media companies keep a presence on the dark web to help users who might, for a variety of reasons, have difficulty accessing their content on the open web. Finally, as with most online accounts, fraudsters bank on the fact that many people still reuse passwords across multiple accounts, especially those they use often like Facebook. Genuine physical identity documents, such as passports and drivers licenses, are incredibly valuable for identity theft. Typically this means fraudulently opening lucrative lines of credit in the passport-holder’s name, which is then swiftly drained, leaving the unwitting victim with a huge debt.
Microsoft Authenticator Requests Exporting Passwords Before July
Darknets also serve as a platform for whistleblowers and privacy advocates. Platforms like SecureDrop enable individuals to submit documents and communicate securely with journalists, thereby exposing corruption and wrongdoings while preserving their anonymity. The significance is in safeguarding the right to free speech and the role of the press as watchdogs. Businesses should be aware of the potential for data leaks and invest in data loss prevention measures. BidenCash and other exit-scam markets such as Torzon and Kingdom Market collapsed between 2022 and 2024. They used “free data dumps” and emotional marketing to build trust before vanishing—an enduring lesson in the risks of social engineering.