However, integrating disparate protocols risks performance lags, necessitating lightweight designs like DeepSearch’s. Its JavaScript reliance sparked privacy debates, but its ~50,000-site index marked a shift toward user-friendly tools. NotEvil’s continued relevance, alongside engines like VormWeb and Tordex, highlighted trends toward safety, community-driven filtering, and innovation. However, other links in the same section were outdated, and one redirected to a suspicious marketplace prompting for crypto.
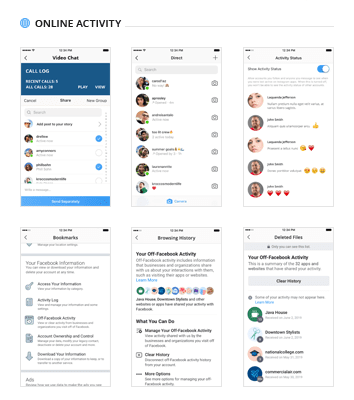
- A VPN hides your real IP address from your internet provider and adds another layer of encryption.
- It is that hidden corner of the internet that is hidden from the public and can only be used by a limited number of people.
- Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
- If a search engine lacks these safeguards, consider switching to a more secure option.
Tor Links
Not Evil is a popular dark web search engine recognized for its extensive database of “clean” .onion sites that don’t contain illegal content. It’s designed with a strong focus on user privacy, as it does not track search queries or gather any personal information, enhancing anonymity. And it also operates without ads, which can be particularly helpful when navigating the dark web.
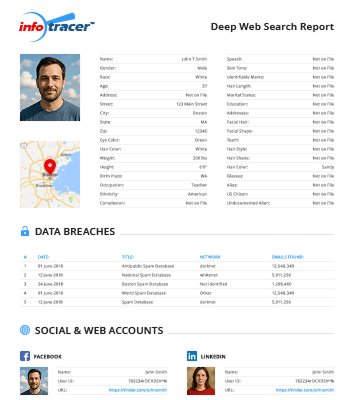
With a focus on providing access to cutting-edge information and resources, Black Hat Search is a valuable tool for security professionals and enthusiasts. DeepNet Explorer is a Deep Web search engine that specializes in indexing and categorizing hidden web content. With a comprehensive database of Deep Web sites and resources, DeepNet Explorer makes it easy for users to find the information they are looking for quickly and efficiently. DarkSearch is a cutting-edge Deep Web search engine that prioritizes user privacy and security. With advanced encryption protocols and a user-friendly interface, DarkSearch is quickly gaining popularity among Deep Web users who value anonymity and protection.
Tips To Stay Safe When Using The Dark Web
However, time has changed, and now several services offer free dark web access with the least amount of technical knowledge. Tor Search constantly crawls (onion) websites 24 hours a day, 7 days a week. In addition, it also revisits already indexed sites to update discover and remove downed and offline sites. However, to maintain the servers, they offer the possibility of inserting advertising banners on their home page.
Safety Tips For Dark Web Exploration
It also offers works of art, course material, and audiobooks for download. Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to “join” your transactions with others to increase your anonymity. We also made sure to select only sites that have been around for a considerable amount of time without being taken down or being the subject of any privacy or security scandals. It is a good website for finding out which websites are currently working. If you need a listing of currently active websites, contact their support, and they will provide you with that.
Most Proven Tips To Increase Your Online Art Sales
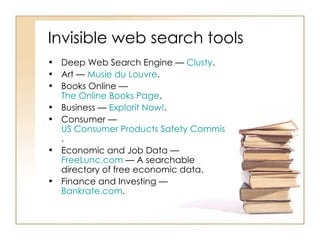
Dark web engines crawl and index .onion domains with ad-free interfaces and privacy protections. Before exploring, make sure you’re familiar with the laws in your jurisdiction. Even someone’s accidental exposure to illegal content can result in them experiencing legal consequences. Before downloading a file, ensure it’s from a reliable and verified .onion site.
The website’s articles focus on digital rights, surveillance, and security research. I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. Using a dark web monitoring tool saves you from doing manual searches and helps you spot threats automatically. It gives you peace of mind, knowing that both the surface and dark web are being watched to keep your organization safer.
However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts.
Visit a known .onion site (e.g., Ahmia’s .onion link) to ensure Tor is working. More importantly, you should now know how to access these hidden sectors of the internet at your leisure. However, if you’re planning to use it for illegal activities, there are significant risks involved. For example, one of the most common ways to access both the deep web and the dark web is through Tor. The dark web refers to the subsection of the deep web that provides illegal services. This runs the gamut from illegal substances to personal information, credit card details, child sexual abuse material and, allegedly, assassination contracts.
Facebook Onion Site
- Regular system audits and avoiding executable files further reduce infection risks.
- The most interesting thing about NordVPN is its built-in Onion over VPN feature.
- It’s a hidden collective of sites that you could only access through a special browser.
- Purchases through links on our pages may yield affiliate revenue for us.
- Privacy-focused internet users who access onion sites may see greater anonymity while browsing or sharing sensitive information.
In January 2025, it held a 0.40% market share in the generative AI chatbot sector, and its website received around 5.50 million visits. Copilot’s website receives more than 67M visits per month, but it’s unclear what the actual number of active users is. Copilot can assist in writing text, performing data analysis within Excel, and providing code assistance through GitHub.
Cybersecurity Vs Web Development: Which Is Better?
You can also check out this ultimate dark web safety guide to browse safely. OnionLand combines the functionalities of both dark web and deep web search engines, providing an intuitive user experience along with access to numerous hidden services. Both DuckDuckGo and Ahmia are safe choices for finding Tor Browser links without being tracked. Any onion websites you visit from these search engines is another story. Dark web websites are pages that exist on a part of the internet that isn’t indexed by traditional search engines like Google. Also known as deep web sites, these pages typically have URLs ending in .onion and are only accessible through special software like the Tor Browser.
Meanwhile, new options have emerged, trying to fill the gaps left behind. 🛒 From tech insights to tools that protect your digital life, Cyber Shop Cyprus is your go-to for all things cyber. 🔍 In this guide from Cyber Shop Cyprus, we’ll introduce the Top 5 Dark Web Search Engines You Can Trust.

Beyond Tor: Other Privacy-Centric Networks
The dark web is a hidden part of the internet that requires specialized software to access. Where you can find all the resources you need to expel Google from your life. Due to the sanctions, upcoming Huawei Android smartphones couldn’t use Google, so the company decided to create their own independent search engine.
Similar to DuckDuckGo, Haystack prioritizes user privacy, pledging not to track data or compromise privacy for profit. Ahmia emerges as a robust dark web search engine offering more than just search results. It provides users with access to statistics, insights, and news about the Tor network, rendering it an invaluable tool for those venturing into the depths of the dark web.
In 2024, I used Haystak’s premium tier for an article on dark web marketplaces. Searching “crypto scam forum onion” yielded a niche .onion site discussing Bitcoin fraud, with active user threads that Ahmia and Torch missed. I’ve relied on them for over a decade to uncover everything from obscure tech blogs to leaked datasets, and their evolution mirrors the dark web’s growing complexity.



