SurfWax is available as a free search and subscription-based service. Aside from basic search, this search site includes several other features. Along with the main search, there are options for blog search, ‘Wikipedia search, RSS feeds search, News, and shopping search. It is the first and easiest-to-use tool for dynamic search query refinement. Elephind.com allows family historians, genealogists, and scholars to browse historic newspaper archives from worldwide.
Darknet Communications In 2025 – From IRC Forums To Telegram Crime Networks
Since Tor has to pass your traffic through several nodes, it will slightly slow your speeds. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. Today, many organizations exist that are created only to handle these reports anonymously and effectively.
- Each expert system specializes in distinct datasets or query types, enhancing the overall accuracy and depth of search results.
- Continuous benchmarking drives ongoing improvements, keeping it ahead in user satisfaction and relevance.
- Impreza Hosting is a service that helps you host a site on the Tor network.
- These practices not only safeguard your personal information but also enhance your overall browsing experience.
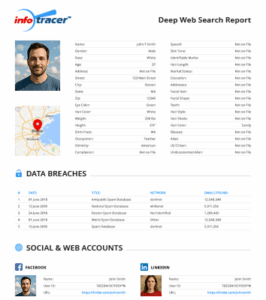
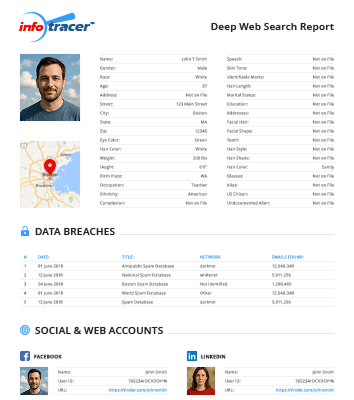
- MyLife pulls data from public records, social media profiles, and other sources to create detailed reports on individuals.
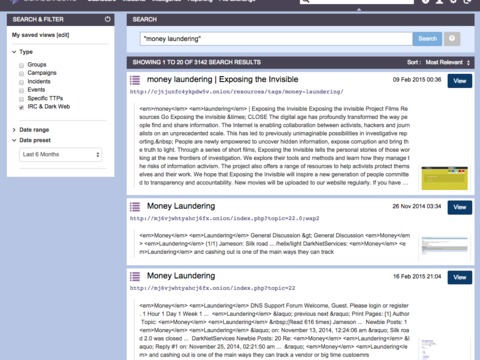
It’s a hidden collective of sites that you could only access through a special browser. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity.
Country Specific Data

Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden. With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity. The wallet is user-friendly and provides robust security, making it one of the best crypto wallets on the dark web. Finally, Wasabi Wallet is non-custodial, meaning you alone can access the encryption keys.
Best Deep Web Search Engines You Can Use
Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. For example, it maintains your privacy and enables you to access untraceable content and services. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.
- The BBC news website has a special .onion site, which you need to access via the dark web.
- Along with the main search, there are options for blog search, ‘Wikipedia search, RSS feeds search, News, and shopping search.
- Its strength lies in regular updates and community-driven verification of links.
- I recommend bookmarking verified links rather than relying on search results.
- Data like this can also help estimate how many people actively access the dark web and how many hidden websites truly exist—you can even tell where the users are accessing from.
Quick Comparison Table: The Dark Web Search Engine Features
In this article, we’ll take a look at how these tools work, how they differ from traditional search engines, and which dark web search engines are most widely used today. Tools like Tor Browser and I2P allow users to explore the hidden layers of the internet, providing anonymity and access to unindexed content. These browsers are often used for legitimate purposes, such as bypassing censorship or protecting privacy. Cybercriminals leverage these platforms to host illegal marketplaces, distribute stolen data, and coordinate phishing campaigns. DuckDuckGo’s dark web version offers the same privacy-focused search experience as its clear web counterpart. What sets it apart is that it doesn’t track your searches or create user profiles, making it ideal for anonymous browsing.

Exploring the dark web can provide valuable insights and essential privacy, but it requires careful, informed navigation. By selecting trusted search engines, crafting precise search queries, and diligently verifying sites, you can greatly enhance your safety and effectiveness. Remember, good digital habits—such as maintaining anonymity, avoiding risky behavior, and staying vigilant—form the foundation of secure dark web exploration. Because deepweb search engines are designed to search specific types of information, they often provide more comprehensive results than traditional search engines. Another benefit of using hidden deep web search engines is that they are often more efficient than traditional search engines.
Although ZeroBin is not an email service, it is a great way to securely share information discovered over the Tor network with friends and other contacts. It’s a straightforward yet effective messaging tool that works by entering text or images into a text field and emailing them to the designated recipient. SecureDrop is an anonymity tool for journalists, lawyers, and whistleblowers. As a source, you can use the SecureDrop installation to submit documents to the organization as a source anonymously.

How To Stay Safe On The Dark Web
It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. Set Tor Browser’s security level to “Safest” for critical dark web activity.
Torch Search Engine
It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. All in all, it is not illegal to access the dark web, but it can create issues for you. If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks.
A Dark Web Search Engine
Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data.
DuckDuckGo has a dark web version that is accessible through the Tor browser. It provides more privacy than regular search engines, but it mostly indexes the surface web and is not specialized for deep or dark web content. Most dark web search engines rely on these crawlers, but some also utilize manual link submission.
However, please note this article is for research and educational purposes only. The dark net is full of notorious hackers, scammers, malware, and other viruses. We recommend using NordVPN and a robust antivirus like TotalAV to keep you safe while browsing the dark web.