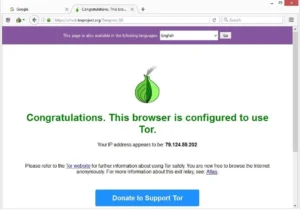
While it’s not 100% foolproof (no directory is), the Hidden Wiki helps minimize risks and provides a safer entry point for users who are new to the Tor network. Yes, a VPN enhances your online privacy on the Dark Web by sending your traffic through its private server network and encrypting your connection. However, not all VPNs come with robust security and privacy features, so make sure to use a premium VPN that won’t leak your data on the Dark Web.
BBC News /somali Somali
These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. Countries differ in how aggressively they monitor Dark Web activity. In some authoritarian states, accessing Tor nodes can flag you for surveillance. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.
Why Our Site Is Better: Up-to-Date, Secure, And No Tracking
The value of a bitcoin is subjected to extreme fluctuation and fell from $145 to $109 that month. These forums are frequently accessed via the top 10 dark web search engines, serving as essential resources for information and networking. If one tries to visit the dark web with a regular browser, there will be no web pages to visit. Since the dark web is hidden from the surface web, these dark web search engines allow users to explore the concealed part of the Internet. But if you cannot access onion sites using your regular browser, how do you find active onion sites?

KeyBase combines encrypted messaging with secure file sharing and identity verification. Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer. DigDeeper offers in-depth analysis of technology and privacy topics rarely covered by mainstream media. The website’s articles focus on digital rights, surveillance, and security research.
Step 3: Enhance Your Anonymity And Security
And because they aren’t searchable via Google or Bing, onion site lists are important roadmaps to help users find what they’re looking for on the dark web. Our meticulous reviews, based on hands – on experience, are designed to assist businesses in selecting the right tools for growth. Whether it’s evaluating the effectiveness of marketing software or the security features of digital wallets, our reviews are a reliable resource for those in the know. No, while the Tor network does host some websites that offer illegal goods or services, many sites are legitimate platforms dedicated to privacy, free speech, and open-source projects. From the latest news on Darknet Markets to tutorials on how to access certain .onion sites, DeepDotWeb offers a comprehensive resource for all things related to the Tor network. To access onion sites, users need a stable internet connection and the Tor browser.
Users can explore onion sites easily and search for content without having to know any specific onion links in advance. You’ll keep your identity private while getting results for various Tor websites, forums, and marketplaces. You’ve probably heard of the “dark web” and wondered what exactly it is and how people navigate its hidden corners.
Never Share Personal Information
But if you use antivirus software, avoid clicking shady links, and stick to known sites you should be okay. It’s also a good idea to set up a VPN for an extra layer of protection. Since the dark web isn’t indexed by standard search engines, sites like Ahmia act as modified directories to help users discover onion sites. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017. You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it. Onion sites, or dark web websites, are sites on the dark web that can typically only be accessed using special software like the Tor browser.
- The vast expanse of the internet is like an iceberg, with a significant portion of it hidden beneath the surface.
- ZeroBin encrypts and decrypts text in the browser, so their servers have no way of knowing what’s happening on the browser side.
- It doesn’t use JavaScript, which goes a long way toward keeping you anonymous.
- Use platforms like Dark.fail or Onion.live to check uptime, domain authenticity, and community trust levels before accessing a dark web site.
- There’s even an option to set a timer on your most sensitive messages so they disappear after a set time period.
Malicious Software

We are reader supported and sometimes earn a commission if you buy through a link on our site. Its dual presence on the surface and deep web, paired with a formal structure, makes it a mainstay among high-level dark web forums. However, you’ll find computer code experts, people searching for adult dates, and other interesting individuals.
We have never received a compensation in any form for operating this website. We are not responsible for any harm or loss you may receive by following links listed on this site. On the one hand, this is considered beneficial for people living under strict regimes where censorship is common.
Top 21 Dark Web Resources Every OSINT Professional Should Know In 2025
The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials. It also includes any content that its owners have blocked web crawlers from indexing. Standard search engines index these websites and are accessible without special configuration.
The Guardian Tor site is a mirror of its regular Tor site, offering the same news, analysis, and opinion as its regular web portal. Proton VPN, in particular, is an invaluable tool for bypassing state censorship, which is why access to the Proton website is often blocked by repressive governments. While it can’t know your real IP address, it can see your unencrypted data, which may reveal your true identity (although HTTPS(new window) still protects you). It includes everything you need to go through a login page to access, such as webmail accounts, social media pages with restricted access, online banking sites, web forums, and much more.
The Top Darknet Markets – Quick List

It boasts a vast archive of over 400,000 pages, providing comprehensive coverage of .onion sites, including forums, blogs, and marketplaces. Beneath the surface web that you’re reading right now, many .onion websites remain invisible to Google and other search engines. These “dark websites” significantly enhance your browsing capabilities, but you can’t access them on a regular browser. Instead, this list includes useful, legitimate deep and dark web websites that are easily accessible from Tor browser. Dark web websites are not indexed by standard search engines and can only be accessed using specialized tools, such as the Tor web browser. These sites provide a level of privacy and anonymity unavailable on the surface web, offering content and goods that cannot be easily found through traditional online platforms.
Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces. Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it. Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. Changing the Tor browser settings can further boost your security levels on the dark web shops.
What’s The Risk Of Clicking Unknown Links On Dark Web Engines?
This is a blog with cybersecurity tips created by the Electronic Frontier Foundation (EFF), a popular non-profit that specializes in digital privacy. The blog contains tons of useful guides about how you can avoid online surveillance. SecureDrop protects your privacy by encrypting your data, which makes it unreadable. Also, it doesn’t log your IP address or any information about your browser or device.
Moreover, due to its popularity, many copycats of the Hidden Wiki exist. So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. Using the Tor browser is simple, but knowing when to fire it up is more complicated. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual.