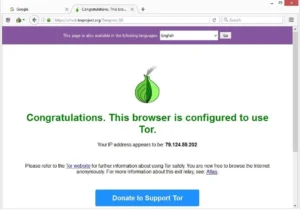
Yes, but only from the sites you connect to — instead of your IP address, they will only see the IP address of a Tor server. That said, using the Tor browser is not 100% safe, as the Tor network has a few security issues. That’s why I strongly recommend using a VPN together with Tor to protect your privacy. I strongly recommend avoiding unofficial sources, as you risk downloading malicious software. All you need to do is visit the Tor browser webpage and click the Windows icon, leading to the installation process.

Is The Tor Browser Secure?

Instead, I2P uses its own brand of hidden sites called “eepsites”. Then there’s the less popular VPN over Tor, which is advised against by the official Tor Project. Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds. Internet traffic first passes through the Tor Network, and then through the VPN. This means the VPN provider doesn’t see your real IP address and the VPN protects you from those bad exit nodes. However, the software that popularized the dark web is The Onion Router (Tor), which launched on September 20, 2002.
Related Articles From The Safe Browsing Section
Instead of the onion routing Tor uses, I2P relies on unidirectional tunnels and garlic routing, which bundles multiple messages together for better traffic obfuscation. It uses its own internal DNS to access “eepsites”, not .onion addresses. This setup is easy to configure, and you don’t need any special settings or features. Just turn on your VPN, wait for the connection to stabilize, and launch Tor.
What Challenges Does Tor Face Regarding Legal Accountability?
It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions. ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023. Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it.
- This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers.
- One of them is called Brave, which is super fast and also blocks all ads and trackers by default before your website even loads.
- With the right knowledge and precautions, you can explore the dark web with enhanced privacy and security.
- As discussed earlier, configuring Tor Browser’s security level is paramount for safer browsing on the dark web.
More Ways To Stay Safe On The Dark Web
It boasts a vast archive of over 400,000 pages, providing comprehensive coverage of .onion sites, including forums, blogs, and marketplaces. Once connected to Tor, you’re ready to begin exploring the dark web. However, keep in mind that the dark web is not organized like the regular internet. Instead of search engines, you’ll need to rely on directories or specific .onion links. In many places, including the U.S., the UK, and the EU, accessing the dark web is legal for legitimate purposes. However, many sites on the dark web host illegal content or activities, and engaging with those can lead to serious legal consequences.
How Can I Differentiate Legitimate Services From Scams On The Dark Web?
Next, hit the New Circuit for This Site button to connect to a different server chain. Repeat this process until you get an IP address from your desired country. If you want to surf .onion sites, see our list of the best dark web sites in 2025. Next, open the Tor browser app and wait for it to connect to the Tor network — this usually takes 5–10 seconds depending on how fast your internet connection is and how overloaded the Tor network is.
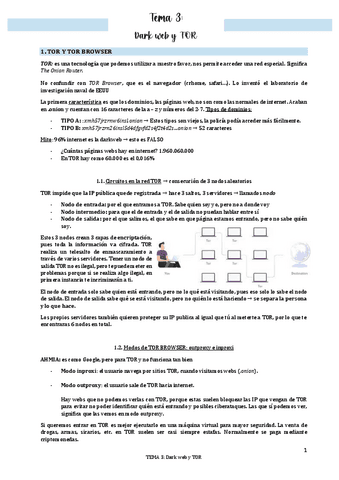
Tor is a network designed to route traffic through multiple servers. The Tor Browser is a specific web browser, based on Firefox, that utilizes the Tor protocol to enable private browsing. Tor routes data through at least three servers, and websites will only see the IP address of the last server, not yours. It has features to maximize your privacy, unlike standard web browsers that have less stringent privacy protections.
A VPN is an online app that also changes your IP address and encrypts your traffic — but it only does it once, which allows VPNs to provide much faster speeds than Tor. To secure your data with a VPN, you use a VPN app (also called a VPN client) to connect to a VPN server. Once connected, the server will route and encrypt all of your internet traffic. Most top VPNs have paid subscriptions, but there are also a few providers that have good free plans that let you test their services. And unlike the Tor browser that only secures the traffic that passes through it, a VPN secures all of your device’s web traffic. With all the identity theft and privacy invasion out there, it’s no wonder people are looking for new ways to stay anonymous online.
- Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously.
- Unlike the publicly accessible surface web, the deep web includes sites requiring login credentials but is still accessible via traditional browsers.
- Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds.
- The deep web is made up of content that search engines such as Google do not index.
- Opinions expressed herein are those of the authors and not necessarily those of Analytics Insight, or any of its affiliates, officers or directors.
- This segmented design makes it extremely difficult for any observer, whether it’s a website, ISP, or malicious actor, to trace your traffic back to you.
Step-by-Step Guide To Accessing The Dark Web Safely With Tor (
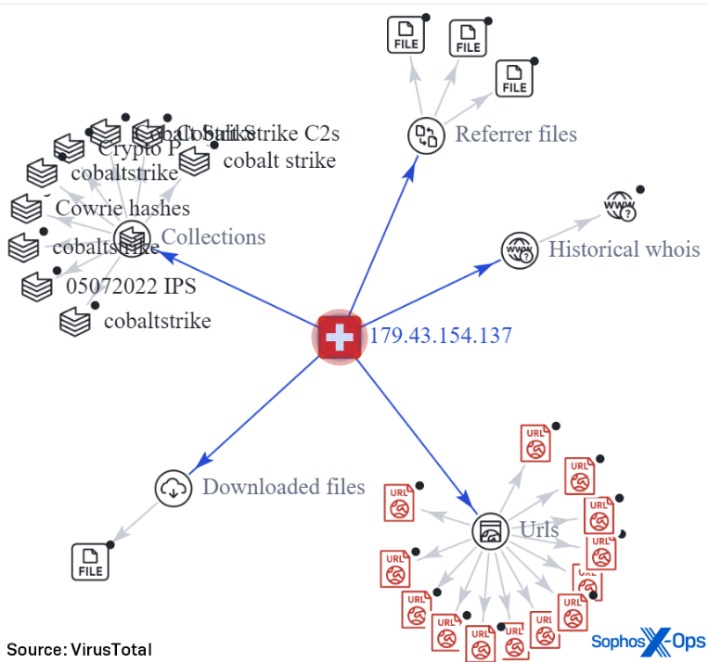
Security professionals monitor the dark web forums not only for real-time threat updates and signals, but also as a direct contact with how the cybercriminals operate and think. Best Hack Forum (BHF) is a Russian forum that’s been operational for several years and accessible through Tor and the surface web. It’s a hotspot for cybercriminals as it covers almost everything about illicit activities.
Despite these methods, finding reliable and safe onion links remains a significant challenge. The decentralized and often unregulated nature of the dark web means that there is no central authority vetting websites or ensuring their legitimacy. Many links found online may be outdated, leading to defunct services.

Getting some of the best free antivirus software can keep you covered in case you make a mistake. Tor’s entry nodes know your browsing IP, and the middle nodes know the location of the entry and exit nodes. If any of the nodes are compromised, your identity might be pieced together.
Internet service providers may also be suspicious of Tor usage and might monitor traffic patterns, even if they cannot see the content of the encrypted communications. Therefore, while Tor provides a strong layer of privacy, it is not an absolute shield against surveillance, and users should remain aware of this possibility. One of the most frequently recommended security measures is to use a Virtual Private Network (VPN) in conjunction with Tor Browser, a practice often referred to as “Tor over VPN”. While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP. A VPN encrypts this initial connection, making it more difficult for the ISP to detect Tor usage. Some VPN providers offer “Onion over VPN” features, which route traffic through the VPN’s servers and then into the Tor network, providing a convenient way to access onion sites.
Perhaps that’s their option for generating consistent traffic and a steady influx of new members. Perhaps its strong community is helping the administrators to keep the forum alive after all the attempts by authorities to seize. Despite all the attacks, blocks, and the constant pressure from the authorities, the forum remains active. However, we’ve compiled a list of the 13 top ones that are worth monitoring in 2025 for cyber threat intelligence. Purchases through links on our pages may yield affiliate revenue for us.
This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels. Check out my article for more information about the dark web and how to access it while staying safe. One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web. The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software (such as the Tor Browser), configurations, and authorization to access. Arguably, the best-known tool used to access the dark web is the Tor Browser. In addition, NordVPN offers Onion over VPN (think Tor over VPN), which routes your internet traffic through one of its servers, passes it through the Onion network, and then sends it to the internet.
You could be monitored closely even if you are not doing anything illegal. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble.