Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security.
The many ways in which stolen data can be misused are complex and do not end here. The increase in data breaches and data leaks has led to more personal data being available for trading on the darknet. This is also reflected in a study, according to which the distribution of stolen data increased elevenfold between 2015 and 2021.
Meanwhile, AI-powered surveillance tools will become a staple for both attackers and defenders in this hidden economy. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Tor is the most popular instance of a darknet,19 and it is often mistakenly thought to be the only online tool that facilitates access to darknets.
Over the following years, it attracted a massive following, becoming the largest darknet platform of its kind by 2024. It offered a broad catalog of illicit goods, including narcotics, counterfeit documents, cybercrime tools, unlicensed pharmaceuticals, and infrastructure-as-a-service accounts. In one particularly devastating case, a man lost his entire $80,000 pension. Using his credentials, cybercriminals committed a variety of online fraud activity over the course of six months. Dread is a Reddit-like forum on the dark web where users discuss cybersecurity, marketplaces, tools, and underground activities.

Disgruntled Developer Gets Four-year Sentence For Revenge Attack On Employer’s Network
On a smaller scale, Mega Darknet Market placed a few ads with QR codes in public places like Moscow subway trains. While tactics like these may have helped boost revenue for both markets, again, they have yet to match Hydra’s sizable financial success. The chart above shows that, while values haven’t risen back to 2021 levels, darknet market revenue has slightly rebounded since Hydra’s closure in 2022.
Best Dark Web Sites In 2025 (Unseen Onion, Tor Links)
Onion sites are websites on the dark web that use the ‘.onion’ top-level domain. They can only be accessed through the Tor browser, which encrypts your connection and masks your IP address, providing anonymity. Discover how to explore darknet market links safely while ensuring your privacy and security. How darknet actors migrated from IRC forums to Telegram networks in 2025. Sellers who deliver the goods on time receive higher ratings and a better reputation over time. Darknet markets offer sellers and buyers resources on how to get their products through the mail, such as what supplies are needed to disguise shipments and techniques to avoid detection.
Do I Need A VPN If I Access The Dark Web On My Phone?
Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack.

Where Can You Find DDoS Services And Tools On The Web?
While many dark marketplaces have been shut down by authorities, new ones soon appear in their place. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. STYX MarketSTYX Market, launched in 2023, is all about financial crime.
What’s The Risk?

Freenet is still an experiment designed to resist denial-of-service attacks and censorship. When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity. For built-in Tor over VPN functionality, NordVPN operates specialized servers that automatically route you through the Tor network. You don’t even need to use Tor Browser, but keep in mind other browsers can still pass identifying information through the network. Alternatively, there’s IPVanish who claim to be the world’s number one VPN for Tor and comes highly recommended, you can save 60% on the annual plan here.
How To Stay Safe From Dark Web Threats
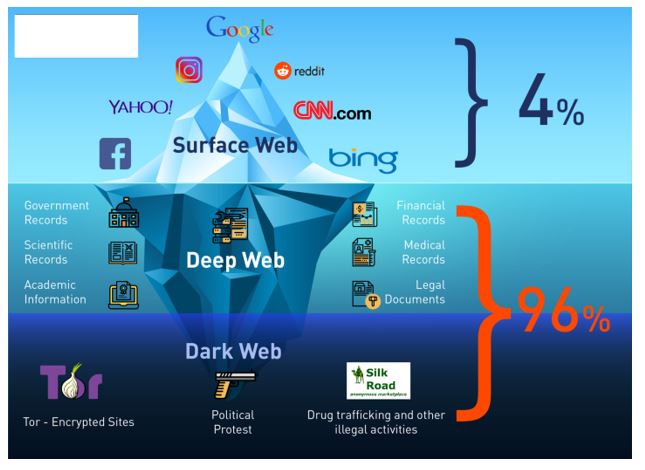
The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited.
Law enforcement agencies have been making significant strides in taking down major dark web marketplaces in recent years. One of the biggest recent successes was the takedown of Hydra Market, considered one of the largest dark web marketplaces. Here, German authorities, along with international support, seized the platform’s servers and confiscated approximately $24.6 million worth of Bitcoin.
For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine).
Can I Use Tor To Browse The Surface Web?
These listings were sometimes very expensive (over $9,000 in one instance) and promised to share details of vulnerabilities that would net the buyer many thousands of dollars profit. We found a wide range of digital templates for bank statements, utilities, passports, pay stubs and driving licenses with detailed guides on how to use them effectively. The typical price for these digital files was $13.97, reflecting their value when used in combination with stolen personal data to open lines of credit. It’s possible to access such software for free on the normal web, so dark web vendors sell cheaply ($3) and tend to offer bundles including additional resources and even customer support to tempt buyers. This software is intended for testing and improving the security of your wireless network by brute forcing passwords and sniffing the data being broadcast. It may be illegal to use it on a network without permission from its owner but that won’t stop hackers determined to steal your data.
- It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks.
- Due to being the most popular and the oldest coin, Bitcoin is traceable.
- Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers.
- Exodus Marketplace started to become popular after the shutdown of Genesis Market, and it replaced it successfully.
- As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.
All Markets At A Glance
Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. A study, Into the Web of Profit, conducted by Dr. Michael McGuires at the University of Surrey, shows that things have become worse.
FAQ – Dark Web Markets 2025 And Cybersecurity
Keeper has millions of consumer customers and the business solution protects thousands of organizations worldwide. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services.