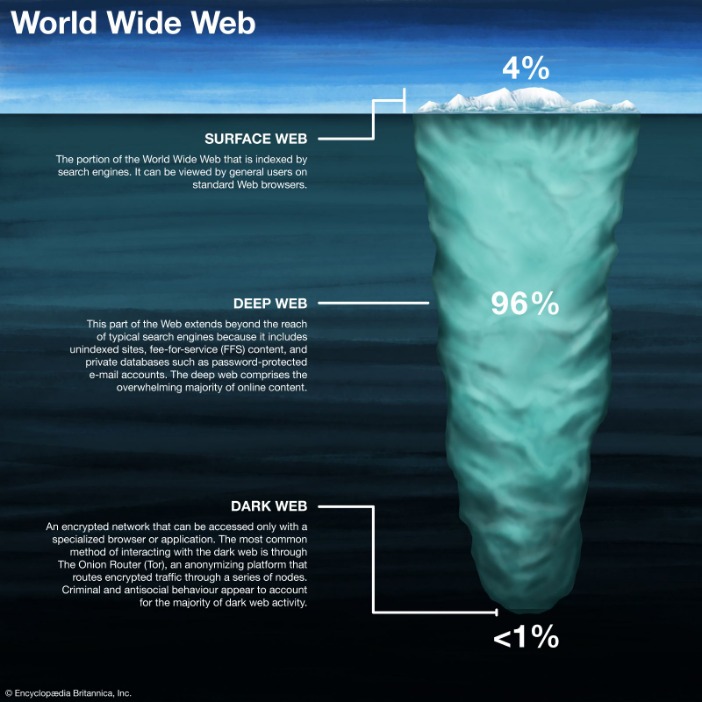
In fact, these supposed “dark web” browsers are not tethered exclusively to this portion of the internet. Many users now leverage Tor to browse both the public Internet and the deeper parts of the web privately. Locating surface web websites is possible because search engines can index the web via visible links (a process called “crawling” due to the search engine traveling the web like a spider). The Internet is sizable with millions of web pages, databases, and servers all run 24 hours a day. But the so-called “visible” Internet (aka surface web or open web) — sites that can be found using search engines like Google and Yahoo — is just the tip of the iceberg.
Discovered pages are indexed in an extensive database and ranked based on numerous factors. When you search a term (or query) in a web browser, the search engine combs through the database to find relevant results and serves them up on SERPs. These sites are intentionally hidden to protect the privacy and anonymity of both the site operators and visitors. No, conventional search engines like Google cannot be used to access the dark web.

The Hidden Wiki — Collection Of Popular Dark Web Links

The current repository has over 20,000 journals with over 10 million articles across all subjects. Although you can easily find free articles on Google Scholar, and it can access some of the information, we think that the DOAJ is a better research tool. Not everything on the web will show up in a list of search results on Google or Bing; there are numerous places that the sites’ web crawlers cannot access. The Flare Threat Exposure Management solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors. We always recommend using a reliable VPN when accessing the deep web or dark web.

Hideme VPN Review: A Reliable Free VPN For Beginners
When you search for something on Google or Bing, you’re using the clear web. Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. At DeepWeb, our goal is to keep you informed about the latest developments in the darknet sphere. From technological advancements to security updates, our expert articles and news updates are designed to keep you at the forefront of industry knowledge.
Add Global News To Home Screen
It does this through automated bots known as crawlers, which start out on websites already known to the search engine and visit every link on said websites before doing the same on the next site, and so on. The deep web — also known as the deep net — is a collective term for non-indexed websites that are invisible to traditional search engines. Because of this, tracking down the web addresses of deep web sites is a much more manual process. Ahmia is one of the search engines designed to be accessed on the Tor browser.
Don’t Stick Your Nose Where It Doesn’t Belong
When you access the dark web, you’re not surfing the interconnected servers you regularly interact with. Instead, everything stays internal on the Tor network, which provides security and privacy to everyone equally. When you envision the dark web, it may conjure up images of hackers trading stolen personal identifiable information or drug dealers advertising their products online—and that’s not completely wrong. While the dark web can be a helpful tool for sourcing legitimate products or ensuring private communication, it’s also a hotspot for illegal internet activity. Offering more than 100 terabytes of data or over 700 billion web pages, it gives you the history of any public site. For most Internet users, the online world begins and ends with Google.com.
What Is The Dark Web, Deep Web, And Surface Web?
It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles. The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily.
BBC Tor Mirror
The Directory of Open Access Journals is a deep internet search engine that provides access to academic papers. Ensuring a secure connection is crucial when browsing the deep web — though Tor encrypts traffic natively, many dark web sites lack SSL certificates. Instead of relying solely on HTTPS, you can verify site authenticity through multiple trusted sources, such as official PGP signatures or well-known directories.
Since the country passed anti-phishing laws, they have issued penalties of more than $1.4 million. Click on biodiversity to access no fewer than 22 sites (directories, portals, specialized search engines, glossaries, etc.). The com (commercial) domain, however, contains sites with less-refined terminology.
- Additionally, you can opt for Subgraph OS as a second option to Tor.
- If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node.
- The deep and dark web may sound similar, but they are not the same entities.
- Getting to the dark web is actually a lot easier than you might think—navigating it is a different story.
- The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China.
More On How To Stay Safe On The Dark Web
Live OS options that can be run on nearly any computer by simply popping a USB stick in and booting from it include Subgraph OS, Freepto, and Tails. Yes, Tor-capable browsers are available for both major mobile platforms, Android and iOS. Now you have enough information about what Tor is, how it works, and how best to use it, allowing you to make an informed choice on its proper use, and how to best protect yourself online when using it. The dark web is a refuge for information leakers and whistleblowers.
VPN Over Tor

Of course, any links and results will not be openable unless you have the Tor browser installed on your computer. Even the regular search engine offers more deep web content than Google. It pools results from more than 500 standalone search tools to find its results. If you pair the regular DuckDuckGo engine with the Onion version, you can perform an entire web search. Unlike Google, Pipl can interact with searchable databases, member directories, court records, and other deep internet search content to offer you a detailed snapshot of a person. To explore the invisible web, you need to use specialist search engines.
Market Value And Popularity
These sites are designed to be easily found and explored by users. In contrast, the Deep Web encompasses all the unindexed and non-searchable content, such as private databases, online banking systems, and academic journals. This hidden part of the internet is not inherently malicious, but it does require specialized tools and knowledge to access.
SecureDrop is an open-source submission system that nonprofit organizations (NGOs), journalists, and news organizations can use to share and receive sensitive files securely. It’s used by 50+ news organizations, including ABC, Bloomberg News, CBC, and The New York Times. However, Facebook’s dark web version will still log your data, so keep that in mind. While your IP address is hidden, the site can still collect information you share on your profile. The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites.
One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web. The dark web (often referred to as the “darknet,” “black web” or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you. The Tor Browser prevents your ISP from seeing what websites you’re visiting, but it does not prevent the ISP from seeing that you’re using Tor. While this doesn’t tell the exit node what your original IP address or your geographical location is, it could spy on your activity if the website you’re visiting isn’t a secured HTTPS website. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting.