We make sure your payment and personal information stay private from start to finish. With us, it’s not just about the product; it’s about protecting your trust. Fraudsters have more tools than ever at their disposal. However, fraud tools like Cloud Passport have likely not examined enough IDs and passports to create truly 1-to-1 fake IDs using AI.
- By staying informed and spreading awareness, you can protect yourself and others from these dangerous operations.
- According to a 2007 study by the National Library of Medicine, 1 in 3 college sophomores, and 1 in 8 high school seniors possess a fake ID.
- “You can’t turn your back on digital for the sake of security.
- As AI generated fake IDs become more realistic and accessible, traditional identity verification systems are struggling to keep up.
When you connect to Tor, your internet activity is sent through the Tor network, anonymizing your Internet activity so it can’t be snooped on, and so that you can access websites that may be blocked in your country. Some states view black and white photos as more resistant to alterations or forgery than color photos, leading them to choose black and white images for increased ID security. Economic factors can influence the decision to opt for black and white photos. Producing these images can be more economical than printing color photos, prompting some states to prefer them as a cost-saving option. Beyond the legal hazards, customers who engage with US Fake IDs have no consumer protection or recourse if their orders fail to arrive or if they receive defective products.
Some establishments employ scanners designed to read barcodes or magnetic strips embedded in real IDs. If you have access, use one to verify authenticity quickly. Furthermore, research apps that help identify fake identification by checking security features digitally.
Need To Change Your E-mail Address?
We accept cryptocurrencies like Bitcoin (BTC), Ethereum (ETH), Litecoin (LTC), and USDT (Tether)—all of which ensure your payment is untraceable and confidential. Our team understands the ins and outs of ID design, including state-specific details, holograms, UV ink, and scannable barcodes. We don’t just create IDs; we replicate them down to the smallest nuances that even professionals can’t detect. Real trust comes from verification that works at scale, resists manipulation, and protects everyone involved. For businesses that want to stay ahead, now is the time to invest in infrastructure that can stand up to what AI makes possible next. Understanding how fake IDs are made is only part of the story.
Understanding Fake ID Websites
That seems very different from other darknet markets. For your safety, always use a new email account for this market, that does not belong to you in any way like name or username. They say, they delete email from their database after you receive your order. Digital Goods, Drugs, Fraud and Guides & Tutorials categories have a large no. of listed products on Elysium Market. This darknet market offers simply UI but there is no advanced search bar like Drug Hub. The interface is very different from all other markets on this list.
PayPal Store
Another dark web vendor that lets you enter in carding/PayPal business. CCPPShop accepts payment in Bitcoin, Litecoin, Ripple and Ethereum. It sells high quality cloned credit cards (EU and US) and PayPal accounts. With each order, you will get a withdrawal guide and socks5 like other carding deep web links. Another hidden service that offers passports, ID cards, and driver licenses.
Common Uses Of Fake IDs
Forums are best places to connect with like-minded people and discuss about any particular topic to get expert/other people views. Below are dark web links of forums which allows you to discuss about various topic like security, drugs, anonymity, software, cryptocurrencies, coding, hacking and many more. It offers gift cards, Debit cards, CC dumps, cash flip, counterfeit, laundering, crypto flip, mixing and hacked wallets. Available cloned credit cards are Mastercard, CCV, US VISA, and VISA.

Identity Verification To Mitigate Threats From Sophisticated Fake IDs
This tactic is especially effective in credit fraud and longer-term schemes that exploit trust over time. At the core of many fake ID tools are Generative Adversarial Networks (GANs). These AI models are trained on large sets of real ID images and learn to produce new, realistic variations by copying their visual features. This includes document layouts, background patterns, barcodes, and the placement of security elements such as seals or microtext.
Ethical And Moral Considerations Of Using Fake IDs And Documents
Because fake IDs can be created quickly and at low cost, fraud can happen at scale—leading to unpaid balances, chargebacks, and drained resources. For many businesses, the financial impact adds up fast and directly affects the bottom line. FraudFighter™ ID (formerly PALIDIN) offers a robust suite of tools built specifically to meet today’s evolving fraud threats. From a philosophical perspective, individuals who rely on fake documents for personal gain compromise their own integrity, fostering personal moral ambiguity that can permeate other areas of their lives. The choice to utilize a fake ID reflects broader questions of personal ethics, signaling a willingness to place immediate desires or convenience over long-term responsibility and social accountability.
The process took time, effort, and access to specialized equipment. Some of the offshore forgery vendors are extremely good at what they do. We’ve bought dozens of documents from sites such as Abacus, BriansMarket and Torzon. At this year’s International Association of Financial Crimes Investigators (IAFCI) show, we had the chance to put them in front of quite a few Secret Service, FBI, Postal Inspector and police officers. “You can’t turn your back on digital for the sake of security.
Undercover agents create convincing fake profiles, interact with criminal vendors, and conduct controlled purchases. These interactions help law enforcement track the identities and operational tactics of criminal organizations. Given the anonymity and encryption inherent to the dark web, authorities have adapted by developing specialized investigative methods and cross-border cooperation.
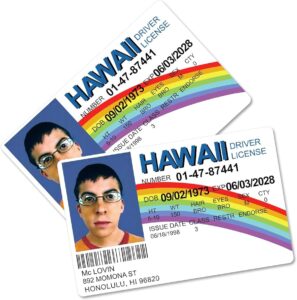
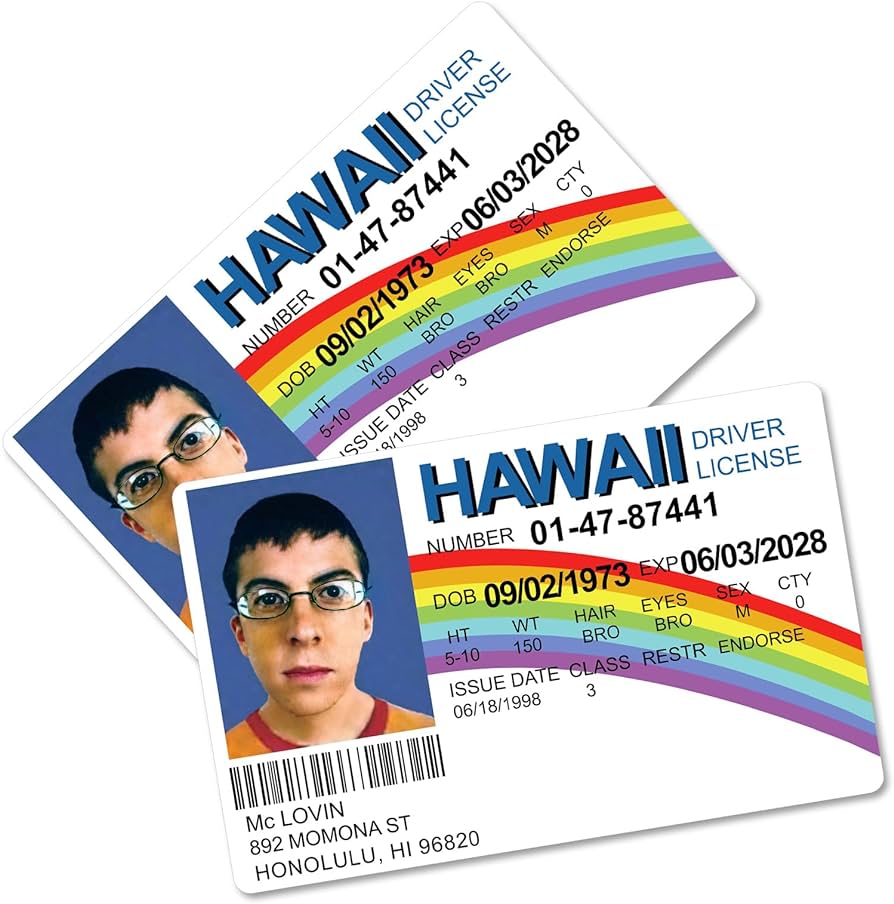
And this study did not look at the countless fake IDs owned and fabricated by fraudsters looking to use fakes for even more nefarious purposes than buying beer. This distinction exists because state IDs are primarily used for identification, while driver’s licenses serve the dual purpose of confirming identity and verifying driving capabilities. Understanding the legal criteria for acceptable State ID or driver’s license photos is crucial. While we guarantee the card will look just like an official ID, the onus for the photo’s quality lies with you. To help, we will offer a comprehensive guide on how to take the perfect photo for your fake ID. When it comes to novelty IDs and gag gifts, FakeYourDrank is a name that often pops up in online searches.
- VerifTools’ homepage warns that it takes no responsibility for what its users do with the generated IDs and advises people to respect their country’s laws and regulations.
- Payment method is Bitcoin like other dark web sites.
- Documents include passport, driver’s license, ID card, SSN, Diplomat, degree, resident permit, and printing documents.
- It facilitates the buying/selling of everything you expect from such a market.
- Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in.
IDScan.net offers the leading adaptive AI identity verification platform focusing on ID fraud prevention, age verification, and access management for security and compliance. From alcohol delivery and online gaming to social media and adult content platforms, age restrictions are enforced by law in many regions. If minors use synthetic IDs to gain access, companies can face lawsuits, regulatory penalties, or even industry bans. AI generated fakes make it easier than ever to bypass age checks, creating serious legal and reputational risks for platforms that do not respond.
Victims of human trafficking or organized crime—enabled by fraudulent documents—experience profound and lasting trauma. Document fraud significantly impacts broader society, creating risks far beyond immediate legal consequences for individuals involved. Cybercrime units routinely monitor dark web forums, chat platforms, and encrypted messaging services, collecting intelligence and building digital dossiers on high-value targets. Authorities employ advanced data-mining software, network analytics, and artificial intelligence-driven algorithms to detect patterns indicative of illegal trade or fraudulent document production. Agents often infiltrate dark web marketplaces by posing as buyers or vendors to gather intelligence on illegal activities.