The plight of BTC is that it wants to square the circle by being a store of value and a medium of exchange at the same time. CoinMarketCap takes a look at the functionality, development, use cases and risks of the Lightning Network, a layer-2 payment protocol on top of Bitcoin. A wallet is the most common user interface to the Bitcoin and Lightning networks, just like the web browser is the most common interface for the HTTP protocol. Let’s say Alice and Bob want to to start using the Lightning Network for fast and cost-efficient bitcoin payments.
- Bitcoin, including its distributed ledger technology, (DLT) lead to a new payment system, creating a true digital currency that could be used as a medium of exchange.
- These systems will remain strong and versatile as long as encryption, decentralized management, AI, and privacy-focused payments are innovated.
- A few other suggested solutions are big enough to fix the problem completely.
- The darknet marketplace ecosystem is expanding rapidly, with projections indicating a significant increase in platform diversity by 2025.
Ideally, intermediary nodes shouldn’t know who are the senders and receivers nor how long the route is. Thus, it’s relatively easy for the attacker to link lightning nodes with announced channels with UTXOs on-chain. Lightning was designed so all nodes can make that link when receiving a new `channel_announcement` message. The key factor in deciding if a service is considered a money transmitter or money service business, based on the FinCEN guidelines, is the custody/control factor. If those running a Lightning Node that route payments are considered to hold custody of the funds they are routing, this would potentially lead to Lightning Node operators being designated as money transmitters.
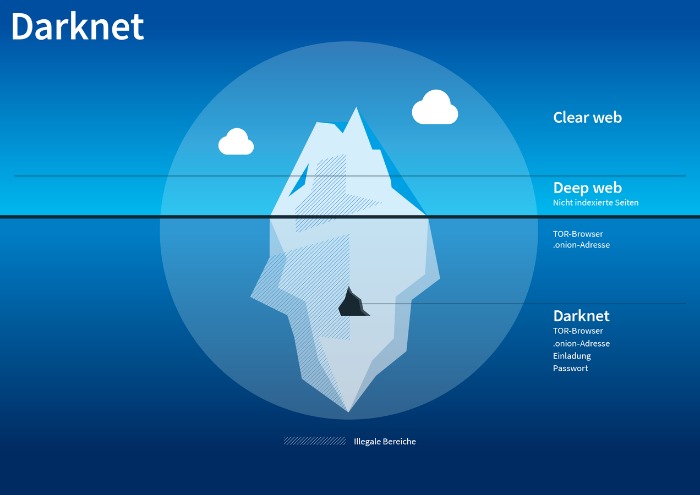
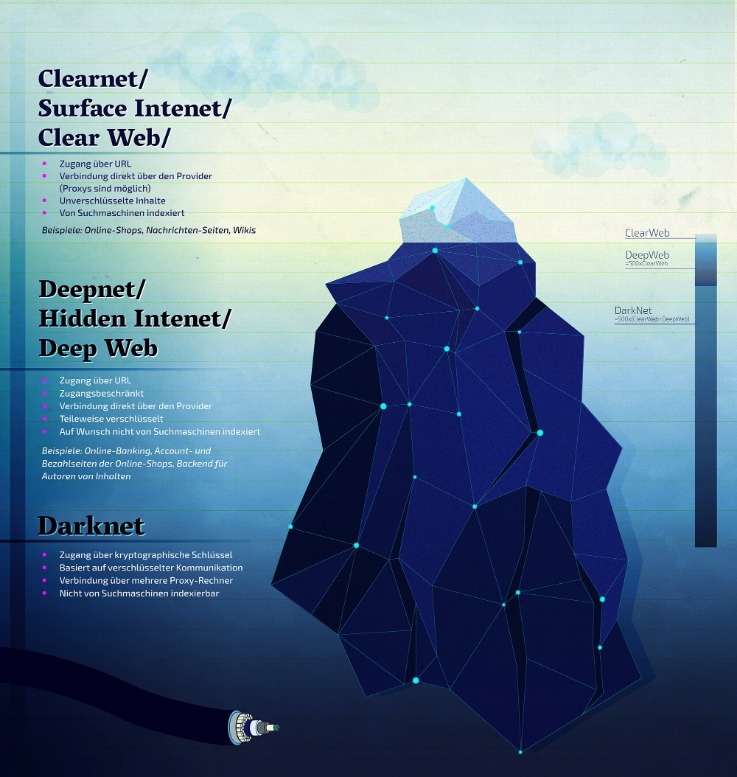
Darknet Marketplaces (DNMs) And How They’re Accessed
To avoid immediate shutdown, the servers hosting DNMs must be in countries with lax legal regulations. This means the server admins must pay significantly higher hosting fees than they would on the clearnet, for less reliable service. Functionally, accessing DNMs and using them requires quite a few extra steps to protect the anonymity of the buyers, sellers, and server admins. To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser.
Security Blogs
As a result, it is possible to conduct transactions off-blockchain without limitations. Transactions can be made off-chain with confidence of on-blockchain enforceability. This is similar to how one makes many legal contracts with others, but one does not go to court every time a contract is made. By making the transactions and scripts parsable, the smart-contract can be enforced on-blockchain. Only in the event of non-cooperation is the court involved – but with the blockchain, the result is deterministic. Nodes have to be able to find each other over the internet to route payments.
Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025
This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. We do not engage with darknet markets; our mission is exclusively dedicated to providing information for research and educational purposes. New markets in 2025 prioritize transparency, with some offering auto-refund for delayed shipments. Buyers can filter searches by trust level, ensuring reliable transactions.
Cryptocurrency: 6 Ways It’s Transforming Everyday Life And Indus
These platforms facilitate access to a variety of goods, with Bitcoin being the primary payment method. Darknet market lists and links help users navigate the ecosystem efficiently. Markets such as Nexus and Abacus maintain reliable onion addresses and URLs, ensuring stable access. The darknet drug market operates with structured feedback mechanisms, promoting trust among buyers and sellers. Trends in 2025 indicate growth in marketplace diversity and improved transaction security.
Nexus stands out for its user-friendly interface and extensive product categories, while Abacus specializes in high-volume sales with competitive pricing. Bitcoin remains the primary payment method, though Monero is gaining traction for enhanced privacy. This information is added to the main blockchain and is called the anchor transaction. It’s decentralized because it isn’t run by a company like Visa and it doesn’t have a leader (Satoshi Nakamoto is long gone, remember?). Bitcoin is run by its users on a network of thousands of computers called nodes. I do not condone the use of DNMs to purchase or sell drugs and other illegal materials online.
How Dark-Web Marketplaces Operate In 2025
Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users. In mid-2024, Telegram confirmed cooperation with European authorities to remove clusters linked to ransomware extortion leaks. While takedowns rarely eliminate operations, they force constant churn and reduce the longevity of large-scale hubs.

Key Takeaways

Escrow systems hold payments until delivery is confirmed, protecting both buyers and sellers. Markets also use PGP encryption for secure messaging, preventing interception. Verified vendors undergo checks, such as sample testing or identity confirmation, though anonymity remains intact. Bitcoin remains the dominant currency in darknet markets due to its decentralized nature and pseudonymous transactions. Its widespread adoption ensures fast, borderless payments without relying on traditional banking systems. Markets prioritize Bitcoin for its liquidity, though some now accept Monero for enhanced privacy.
Providing incorrect shipment information or tracking numbers is prohibited. This tendency makes it harder to shut down marketplaces since they don’t have a single point of failure. Darknet marketplaces push beyond the boundaries of safe digital engagement by constantly improving encryption methods, making it harder for authorities and enemies to intercept or decrypt messages.
Machine-to-Machine (M2M) Payments
The Lightning Network is a groundbreaking solution to the scalability problem faced by the Bitcoin network. The main advantage of the Lightning Network is that it enables fast and cheap transactions by using payment channels that allow transactions to be madeoff-chain. Every public channel announces its capacity (the total amount of Bitcoin locked in the payment channel). But no information is available for how the capacity is currently distributed in a channel. The technique allows a lightning node to “probe” other nodes in the network in order to find how the liquidity is distributed in their payment channels. When a public payment channel is created, the node sends a `channel_announcement` message to other nodes in the network through the gossip protocol.

They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily.
Due to the routing functionality of the Lightning Network, Alice can send funds to Bob through the coffee shop as both counterparties have an open channel with the coffee shop. As per the illustration below, Alice’s 0.01 bitcoin would be sent to the coffee shop, whose Lightning Node would route the payment to Bob. As such, the technology allows for instant, and next to no cost micropayments. Additionally, due to the speed of Lightning transactions, it is estimated that millions to billions of transactions can be processed per second. Using our example, Alice could open a payment channel with the coffee shop using the Lightning Network. We’ll break down how this technology functions by analyzing its key features while using an example (i.e. Alice buying a coffee from her favorite coffee shop) to provide context and clarity.
Any number of transactions between the first and last will occur off-chain. Due to the lack of restrictions within the blockchain, all intermediate transactions happen much faster. Alice and Bob’s bidirectional payment channel is now open and Alice and Bob’s Lightning nodes can start sending each other funds, through what are called commitment transactions. The total amount of commitment transactions cannot exceed the amount of the funding transaction. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet.