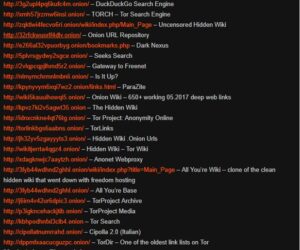
Any site that ends with .onion can only be accessed through TOR. Unlike traditional TLDs, servers using...
wpadmin
Moreover, the layers of encryption and the bounce of your data from node to node effectively mask...
This will ensure that your main machine is protected even if things go wrong. The Tor browser...
If you are looking to do some armchair ghost, UFO or cryptid hunting then check out these...
Then get a VPN to help protect your privacy on dark web websites or wherever you browse...
Borderless news reporting and uncensored media are among the most important and practical uses for the dark...
Its community-driven verification system helps minimize the risk of scams and outdated URLs. Dark.fail also emphasizes user...
Use encrypted communication platforms instead of the standard ones with less robust security features. For example, you...
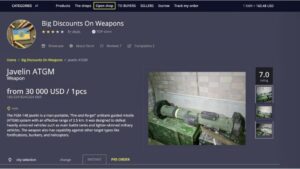
Clicking the wrong link can lead to malware, fraud, or identity theft. Darknet market lists play a...
The only difference is that it passes your traffic through random nodes before reaching the destination. This...