Undercover operations and advanced digital forensics have led to the arrests of prominent dark web figures, sending...
Uncategorized
Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software...
Torch is one of the oldest and most popular onion search engines on the dark web, serving...
Since dark web sites are frequently invite-only, gaining access typically requires infiltration by masquerading as a malicious...
When you purchase using links on our website, we may earn an affiliate commission at no extra...
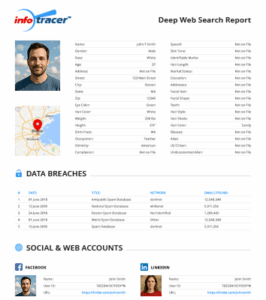
Some sites might use these details for advertising, analytics, or tracking your online preferences. For several years,...
Arrested earlier this year, McCann allegedly shipped over 10 2kilograms of fentanyl and over 300,000 counterfeit Xanax...
Like CrowdStrike, this system requires you to set up a list of identifiers for your company, which...
Intellectual property, including proprietary code, designs, and trade secrets, is a critical asset for many organizations and...
These unique URLs, accessible only through the Tor network, provide an additional layer of anonymity by masking...