There are millions of factories in China that work around the clock to manufacture vast amounts of consumer products for the world. A clip from inside a factory in China has given us another uneasy glimpse into the future of employment as artificial intelligence takes hold. Dark factories use automated air purification systems and dust-removal technology to maintain pristine environments without human contamination. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment.
How Dark Factories Will Shape Global Trade
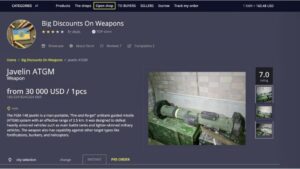
On average, the marketplace consists of more than 11,000 items and 1000 vendors. Besides this, it supports wallet-less transactions and accepts payments through Bitcoins, Litecoin, Monero, and Zcash. However, you must wait some time to reassess this marketplace because it’s been shut down. It issued a press release revealing that, from December 2021, the website won’t be functional anymore. World Market is another largest dark web shops that deals with various goods and services. Its impressive anti-DDoS protection feature and easy-to-use interface make this marketplace stand out among the others.
The Rise Of Dark Factories: China’s Fully Autonomous Manufacturing Revolution
Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims). To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test. Awazon Market is a top-tier dark web marketplace with claims to revolutionize secure anonymous commerce.
“Criminals will always adapt, in the same way governments do,” says Maria Nizzero, a financial crime researcher at the Royal United Services Institute (RUSI). Even Mexican and Colombian drug cartels, who previously kept such activities “in house”, are now using Chinese launderers to service their empires, US lawmakers heard last month. The Italian football referee, who has been accused of moonlighting as a drug trafficker known as “Rambo”, was there to meet a Chinese money launderer who could help him pay suppliers in Spain for a shipment of hashish, prosecutors claim. The market faces challenges such as high initial capital investment, maintenance costs, and complex regulatory environments that can impact growth. Elliptic concluded that if you want to disrupt this ecosystem, it’s going to take a lot more than a couple of channel bans.
The Future: Will Dark Factories Take Over?
Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats. Buyers and sellers frequently face risks from malicious actors posing as legitimate vendors or customers, potentially leading to financial loss or exposure of sensitive personal information. In this article, you’ll find detailed overviews of the top ten Dark-Web marketplaces currently dominating the hidden internet landscape in 2025. We’ll explore their unique features, common use-cases—both legitimate and illicit—and the significant risks users face when interacting with these platforms. The mortality rates from fentanyl consumption and increasing enforcement actions against dealers have even spooked many cybercriminals into steering clear from facilitating its trade.
Power Your Insights With Data You Can Trust
Additionally, the report includes insights into the competitive environment, SWOT analysis, current market trends, as well as the primary drivers and constraints. Furthermore, it discusses various factors that have driven market expansion in recent years. The report also explores market dynamics, regulatory scenarios, and technological advancements that are shaping the industry. It assesses the impact of external factors and global economic changes on market growth. Lastly, it provides strategic recommendations for new entrants and established companies to navigate the complexities of the market. Key market drivers include the rising penetration of the internet and the growing digital transformation across various industries in China.
- They casually disclosed who their acquaintances were in Latin America, some of whom they said lived in Mexico City.
- Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero.
- This significantly enhances the ability to record various crimes more efficiently, allowing automated retrievals.
- We’re talking about even early access to unreleased music, leaked TV episodes, concert footage, and even popular video games before they officially drop.
- Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital environment.
- Self-developed AI systems monitor production live, catching issues immediately before they become defects.
China’s Surveillance State Is Selling Citizen Data As A Side Hustle
With no marketing or advertising, and only a single service—cash for cash—underground banks in China have blossomed into multi-million dollar operations that are able to move faster and more efficiently that regulated Chinese banks. Geopolitical tensions will likely fuel the rise of hacktivism and ransomware in the Middle East. Hacktivist attacks have already evolved from denial-of-service operations to data leaks and critical compromises, a trend expected to grow. Ransomware groups are anticipated to split into smaller, independent units, making them harder to track.
- There is no need to visit darknet marketplaces yourself to know whether your data was leaked.
- We cannot ascertain if the data offered here came from the exposed database mentioned above, as it is a common practice for Chinese threat actors to parse large leaked databases into smaller sizes based on certain attributes in order to monetize it more easily.
- “We welcome elites from all industries who have internal search conditions to join us!
- No relationship is created with you, nor any duty of care assumed to you, when you use this blog.
- An intriguing study 25 provides an overview of current knowledge on prodrug activities on the deep web for mental health and addiction professionals.
- This poses high public health risks, especially when regulatory bodies can no longer control prices and availability.
Key Geographical Areas For Dark Tourism Growth
A study 60 examined trust and reputation building on Darknet marketplaces where vendors and customers exchange illicit drugs and other goods using hidden internet services. They qualitatively analyze data from a study on small-scale drug dealing and case studies on four online vendors. They find trust is established differently online through anonymizing software, cryptocurrencies, escrow services, and customer feedback systems.
Torrez Market
Two novel technologies, i.e., the Tor network (or Onion routers) and cryptocurrency bitcoin, complemented the anonymity requirements of users and financial exchange without traceability. Studies and developments on the use and misuse of the Darkweb are relatively recent, with publications on these topics beginning around 2010. In their study 65, investigated how Darknet market users establish and compare drug quality. They use a two-stage method, analyzing a user forum and conducting qualitative interviews with Darknet users.
Moreover, the market is characterized by a high level of competition among major telecom operators, which can lead to pricing pressures and impact profitability. In countries with similar market structures, the number of telecom operators decreased by 15% over a five-year period due to consolidation and competitive pressures. Additionally, the rapid pace of technological advancements in telecommunications requires constant upgrades to the network infrastructure, adding another layer of operational complexity.
As it turned out, the core of the business consisted of an expansive warehouse with a large laboratory and storage area. The scale of the warehouse was staggering, with hundreds of metal drums filled with chemicals stacked one on top of the other, waiting to be put onto shipping containers. We arranged to meet the owner at a bus station near a major port city in a nearby province. As we walked to the storage space, the owner said we would only be shown limited areas of the business, but that it would include cargo that was ready to be loaded onto a ship.

This marketplace accepts payments via Monero but also supports the Escrow system. This guide outlines different ways of safely accessing dark web stores and the list of reliable dark web marketplaces you can consider visiting in 2025 for research and monitoring purposes. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring. Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats.
Despite the concentration, the market is competitive, driven by the need for continuous innovation and technological advancements to meet the growing demand for high-speed, reliable data transmission. On October 23, 2022, President Xi Jinping secured a third term as the General Secretary of the Chinese Communist Party (CCP) and the Chairman of the Central Military Commission (CMC) at the 20th National Congress, further consolidating his power. President Xi’s speech to party cadres suggests that he intends to firmly implement the zero-COVID policy, which has already seen negative economic and social costs. The slowing economic growth and widespread discontent will likely drive disenfranchised youth into cybercrime due to lack of economic opportunities. We also expect the majority of lower-level Chinese threat actors to continue to conduct cyberattacks against China’s domestic industries including healthcare, financial, government, and education entities for financial gain. More resourceful threat actors will move their cyber operations abroad or focus more on foreign data/access to diversity their portfolio, recruiting foreign cybercriminals to participate in cyberattacks against global entities.