It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. To expand their reach, some marketplaces established parallel channels on Telegram. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site.
Versus Market (Best For User Reviews & Vendor Ratings)
- The allure of the dark web store is strong, yet it is essential for potential users to understand the risks involved and navigate carefully.
- You can also run a dark web scan to see if your information has been leaked on the dark web.
- Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web.
- The products that are most commonly listed for sale include drugs, fake documents, fraud-related items, and hacking services and tools.
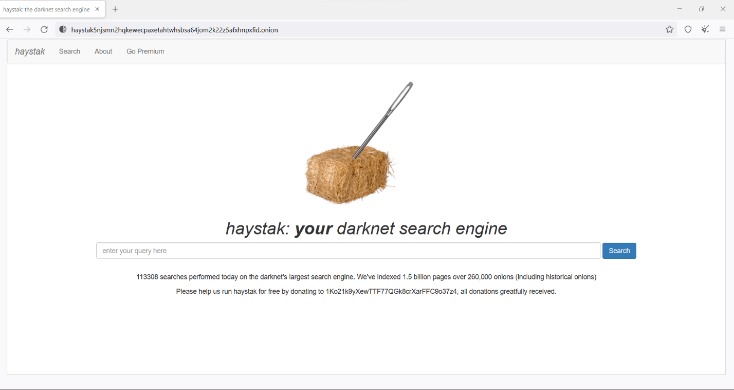
- For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question.
mark it means it has been verified as a scam service and it should be avoided.
|
- Hydra Market’s sales amounted to at least 1.23 billion euros in 2020 alone.
- You risk being targeted for attacks if you explore the dark web without protection.
- Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows.
- Sci-hub is a helpful dark web platform for those looking to access important research blocked by a paywall.
- For small and medium-sized enterprises (SMEs), the consequences of compromised credentials, data breaches, and reputational harm can be devastating.
- Whether or not you’re on the dark web, Facebook loves to collect data.
}
Use Norton VPN to encrypt the data you send and receive and surf more anonymously. KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. Moreover, you can use a Tor circuit, but it won’t improve security; instead, it will surely improve the browsing speed.
Law Enforcement Agency Restores Confidence In Cyber Defenses
For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved. This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation. This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.

What Types Of Content Can I Find On Dark Web Marketplace Links?
OnionName lets you generate an .onion domain name that starts with a specific keyword — like onionamev33r7w4zckyttobq3vrt725iuyr6xessihxifhxrhupixqad.onion/, which is OnionName’s dark web link. The keyword in that example is “onioname,” which is right at the start of the .onion link. With a readable site name like that, people will know what to expect when they click on the link. Darknetlive contains articles about everything related to the dark web. Articles are published regularly and include interesting information, images, and quotes from officials.
Recognizing Common Scams And Deceptive Tactics
By approaching this hidden corner of the internet with informed caution and ethical awareness, you can navigate it more safely and responsibly. One of the most insidious dangers on the dark web is not just technical malware or hidden exploits, but the human element—scammers and con artists who rely on psychological manipulation. Social engineering attacks leverage trust, fear, curiosity, or urgency to trick users into revealing sensitive information, transferring funds, or compromising their anonymity. By learning to recognize these ploys and adopting defensive habits, you can significantly reduce the risk of becoming a victim. While no approach guarantees complete safety, a careful and skeptical mindset serves as one of your most valuable tools on the hidden internet. This article aims to shed light on the more constructive side of the dark web, guiding readers toward reputable resources and reliable information.
Market Types
Exploring the realm of the dark web store can be both fascinating and dangerous. Understanding how to navigate this hidden part of the internet is crucial for anyone considering venturing into its depths. Always prioritize safety, remain informed about the risks, and exercise caution when engaging in any transactions. Another important source of information is the trading cash flow, which is recorded in the block chain and might contribute to a comprehensive view of the supply-demand relationship. We did not include such analyses due to the time and scope constraints, and it is a topic that we plan to investigate further.
Using Escrow And Trusted Mediators Where Possible
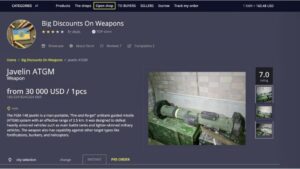
Deep web marketplaces are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity of the dark web. The goods and services on offer range from leaked credit card details, exploit kits, and hackers for hire to advertisements for hitmen services. Brian’s Club has been around since 2014 and remains one of the most well-known credit card shops on the dark web. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data.

Which Darknet Markets Accept Zcash
ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it. Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. While it is not illegal to access the dark web, many of the activities that take place on the dark web are illegal. If you engage in any illegal activities on the dark web, you could be arrested and charged with a crime.
For criminals that want to hack ATMs, special malware is available on the dark web for only $5,000. For this price, cybercrooks can buy Cutlet Maker on the dark web marketplace Alphabay. ATMs are vulnerable when they run on outdated operating systems such as Windows XP or on any other OS that is no longer supported.
Marketplaces For Everything Illegal
Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. Cryptocurrencies weren’t so popular among the general public until recently. However, dark web users have relied on Bitcoin transactions for over a decade, as they allow people to make payments while staying completely anonymous.

DarkNex: Anonymous Dark Web
The platform’s popularity continues to grow, attracting both new and returning customers. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience. Like other marketplaces, ASAP Market also requires you to register for an account.
Today, buyers and vendors look for reliable alternatives that offer security, escrow protection, and a strong vendor community. In Grand Theft Auto Online, players who purchase warehouses and garages for illicit cargo and stolen cars can buy/steal and sell them through trade on the “SecuroServ” syndicate website. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft.
A study by IBM found that 83% of consumers will stop doing business with a company after a major security incident. While no approach is foolproof, a thoughtful, criteria-driven strategy ensures a more secure and beneficial experience on the dark web. As most malware is designed for Windows, another way to stay safe is to switch to a different operating system.