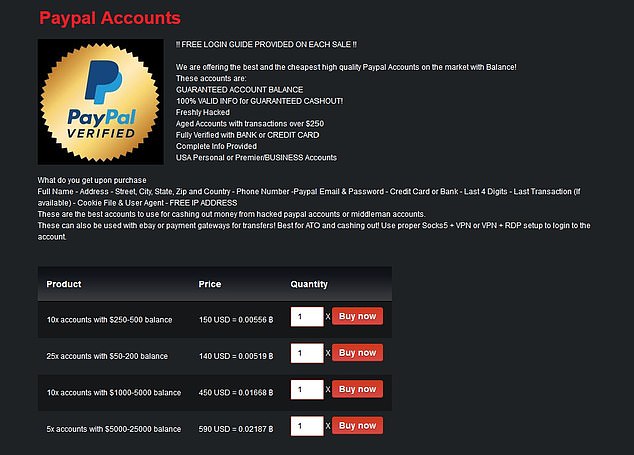
It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts.
MULTI-LAYERED ENCRYPTION

The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed.
- Hackers may threaten to release sensitive information unless victims pay a hefty sum.
- However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities.
- The dark web is not invented for wrong use but to provide privacy and anonymity to whoever needs it for transferring confidential data.
- The Digital Economy Act 2017 requires ISPs to prevent access to these sites and have agreements with foreign countries in order to enable enforcement of these rules.
- The Dark Web and Darknets offer valuable spaces if you value privacy, freedom of speech, or research security technologies.If you misuse them, the consequences can be severe.
First, Install A Reliable VPN
Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays. Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles.
Illegal Pornography
The dark web is home to some horrible stuff; think illegal porn and snuff films, along with illicit activity in the form of financial scams, personal data sales, and other anonymous and illegal transactions. There are marketplaces where people can sell stolen credit card numbers, conduct illegal drug transactions, and scam people out of their cash and crypto. In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
Dark Web’s Share Of Global Internet Traffic
The terms “forum” and “board” may refer to the entire community or to a specific sub-forum dealing with a specific topic. A cache is hardware or software that is used to store something, usually data, temporarily in a computing environment. It is a small amount of faster, more expensive memory used to improve the performance of recently or frequently accessed data.
- The dark web markets and the darknet vendor shops have the tendency to cause exit scam which is fleeing away with the money of the buyers and never delivering their stuff.
- These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information.
- I2P can only be used to access hidden sites that are only available on the I2P network.
- A computer network is a group of interconnected nodes or computing devices that exchange data and resources with each other.
- The dark web is a small, hidden subset of the deep web that requires special tools to access.
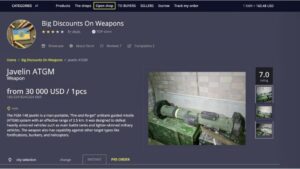
Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers. A study, Into the Web of Profit, conducted by Dr. Michael McGuires at the University of Surrey, shows that things have become worse. The number of dark web listings that could harm an enterprise has risen by 20% from 2016 to 2019. Of all listings (excluding those selling drugs), 60% could potentially harm enterprises.

DDoS attacks have been used by extortionists who threaten a site with offline removal unless a ransom is paid. You typically pay only for cloud services you use, helping you lower your operating costs, run your infrastructure more efficiently, and scale as your business needs change. Investigators and prosecutors need to be able to co-ordinate their approach and respond quickly to developments and opportunities to disrupt or prevent illegal activity, obtain evidence and make arrests. Consideration should be given as to whether a Joint Investigation Team (‘JIT’) is appropriate. Digital evidence and communications data can also be obtained directly from Communication Service Providers (‘CSPs’) as well as from computers and digital storage devices.
See Your Digital Footprint With A Dark Web Scanner
Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen. Simply download the file, install the software, and you’re ready to use its web-based interface.
The CSO Guide To Top Security Conferences
Nathan Bake is branded a “serious danger” to children after acting as head moderator of the website. Hackers may threaten to release sensitive information unless victims pay a hefty sum. This extortion technique can cause significant distress and financial loss. Cryptocurrencies provide an added layer of anonymity, making it harder for your transactions to be traced back to you.
This type of darknet is primarily used for illegal activities such as drug trafficking and pornography. Empire Market is the most prominent online market in the English-speaking community and is the largest marketplace on the dark web in the Western Hemisphere. It is well known in the darknet community for being a trustworthy and anonymous market, which contributes to its widespread appeal as a shopping destination for users of the underground internet. The dark web markets and the darknet vendor shops have the tendency to cause exit scam which is fleeing away with the money of the buyers and never delivering their stuff. All these marketplaces and vendor shops are eliminated what seems scammers or have proof of scamming people. You must also go for dark web vendor reviews or darknet vendor reviews to get a fair idea of the vendor shops you may have chosen.

Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder.
Your data is encrypted in the Tor browser before reaching the ZeroBin servers. ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee.
It may involve computer fraud or forgery, hacking to steal personal or valuable data for commercial gain or the distribution of viruses. In addition to the brief introduction of “fake” marketplaces on the dark web, dark web users visiting political sites on the Tor network should realize that government-funded cyber teams are on the lookout for such users. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites. Meanwhile, Facebook also offers dark web access to their social network. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s.
On the other hand, dealers from Pakistan and Afghanistan sell top-notch hash for this or even lower price. The one which came from the UK cost about $3 per gram and was the worst hash I ever tried – a pale-black waxy substance with a little THC. I paid for the resin from the Asian country $2 per gram and was pleasantly surprised at its potency and fragrance. You’d better always favour domestic dark web trusted vendors over overseas ones for three reasons.