You’ll get stolen credit cards, remote desktop account info, personal details, and various logs. What makes this market popular is the fact that it’s less expensive compared to the rest. The market started in 2021 in Canada and features both international and Canadian users.
Alternative Anonymous Networks
The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. A VPN enhances your privacy and security by encrypting your internet traffic and masking your IP address, making it difficult for anyone to track your online activities on the dark web. It’s essential to use a VPN, like Forest VPN, to secure your data, avoid clicking on unfamiliar links, and never disclose personal information. Additionally, using antivirus software and strong passwords can further protect you from potential threats.
How To Access And Trade On Darknet Markets
The list includes information on each market’s products, security features, and user reviews, making it an invaluable resource for anyone looking to explore the darknet. Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here. The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them. You can see all the product categories the marketplace deals with on the homepage.
Secure Your Connection
Despite enforcement actions, such as Hydra’s 2022 closure with $5.2 billion in seizures, markets like Abacus and Torrez persist, leveraging decentralized systems and blockchain resilience. Market is very similar to Hydra, with the market’s logo on the top left, search bar in the center, and image-linked vendor shops arranged in a table on the main page. To access the marketplace on the Tor network and view vendor’s offerings, market visitors must solve a number and text-based captcha. Hydra also featured numerous vendors selling false identification documents. Users could search for vendors selling their desired type of identification document – for example, U.S. passports or drivers’ licenses – and filter or sort by the item’s price.

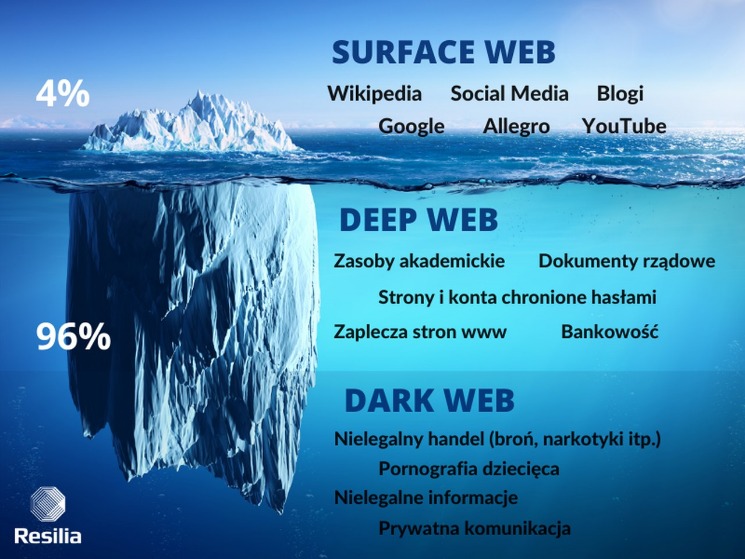
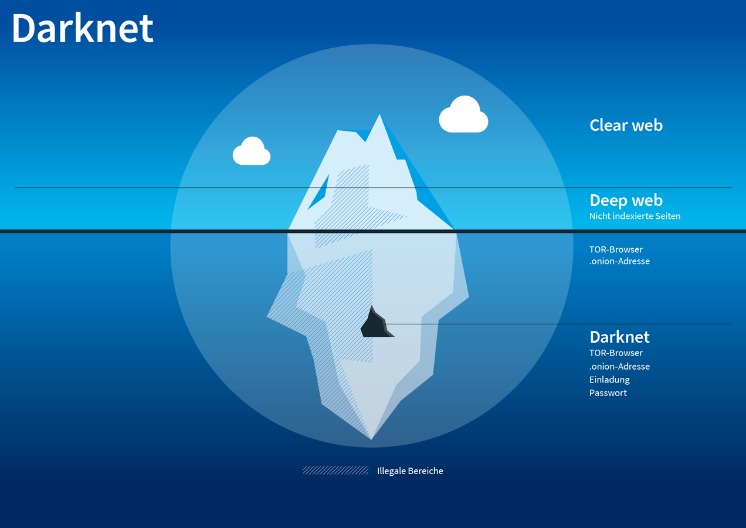
As you delve deeper into the depths of the internet, you’ll encounter a labyrinth of links and encrypted pathways leading to this clandestine marketplace. Torzon, nestled within the layers of the Tor network, is a black market where anonymity reigns supreme and transactions occur in the depths of the deep web. However, your online activity is encrypted and hidden from view thanks to Tor’s onion routing. This means your ISP can’t see that you’re accessing the dark web (or indeed, the specific sites you’re accessing). Put simply, the deep web is all the information stored online that isn’t indexed by search engines.

Staying Up To Date With Darknet Markets
- Gain entry to the Archetyp Market through its secure links and mirrors.
- Dark web markets offer a wide range of illicit items, including drugs, weapons, stolen data, hacking tools, counterfeit money, and more.
- Vice City’s 700+ vendors focus heavily on drugs (80% of its 18,000+ listings), rated 4.6/5 across 25,000+ reviews, with digital goods and fraud tools at 10% each.
- Just as there are new entrants, the dark web has its veteran markets too, and Brian’s Club is one such market.
- Step into the intriguing world of Archetyp Market, where anonymity meets opportunity.
- While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime.
There’s also a search bar that you can use to search for any particular product or vendor. It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities. The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation.
More Search Engines
While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks. The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one.
A Step-by-Step Guide To Access The Dark Web – Trusted Insights From TorConnect
In this ultimate guide, we delve into the intricacies of Torzon, providing you with insights to navigate this hidden realm with confidence. Bitcoin and Monero roll here; I grabbed a cheap tool last Tuesday and had it by Friday. This means that the identities and locations of darknet users are hidden from public view and remain anonymous, even when interacting with other users or engaging in any online activity. There are many different ways to access the dark web, but navigating it can be tricky and dangerous if you don’t know what you’re doing. A VPN will give you an extra layer of protection and anonymity, making it much safer to explore the dark web.
Trusted Directories

Search engines like Google, Bing, and Yahoo can access just about 4% of the web. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Radar Rundown Hiding your IP address is one of the best ways to protect your online activities from …
A VPN, in combination with Tor, further enhances the user’s security and anonymity. That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. Dark net websites are called “Tor hidden services”, and they can be distinguished from normal websites by their URLs. Internet providers and websites can detect when Tor is being used because Tor node IPs are public. Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used.
8.) Now you will see your keyring that contains all the PGP keys of people you have imported, including the one we just imported for this tutorial. Locate the PGP key of the person you wish the message and click “encrypt”. 7.) Your PGP key will begin generating and soon a new popup will appear requested a password for you PGP Key. Make sure you enter a good, strong password, and if it’s not something you can easily remember, make sure to write it down and store it in a safe place. If you lose your password you will not be able to decrypt messages or unlock accounts that have 2FA backed by this PGP key. PGP Encryption is one of the most important and primary aspects of proper OPSEC, especially when navigating or using Darknet Markets.
You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Cybercriminals often use fake darknet market URLs to exploit unsuspecting users. This could involve phishing scams, malware downloads, or financial theft. Archetyp Market is an online darknet marketplace, founded in late 2021. As we approach the year 2024, the dark web markets are expected to undergo significant changes. With new technologies and regulations emerging, it’s essential to stay informed about the latest trends and developments.
The dark web is not a place that you can venture into without protection and caution; a slight slip-up can lead to major consequences. Perhaps, the lack of rules and anonymity of the dark web can be tempting, but those are the same things that make it a risky environment. Moreover, it’s not only the entertainment industry that gets hit; some sell cracked versions of the most expensive software, and others offer pirated eBooks and academic material at cheap prices. The nature of the dark web (anonymity and privacy) opens opportunities for drug dealers to reach a wide customer base across the globe without getting caught.
Its 95% escrow success rate resolves disputes in 36 hours for 90% of cases, securing its 1,500+ vendors and 9% share. Abacus employs AES-256 encryption with mandatory PGP for vendor comms, ensuring data privacy. Optional 2FA enhances account security, adopted by 60% of its 15,000+ users. Multi-layered DDoS protection countered a 2024 attack, maintaining 95% uptime across its onion routing. Its 98% escrow success rate, backed by a 20-person moderation team, resolves disputes in 36 hours for 90% of cases, making it a security benchmark in 2025.



