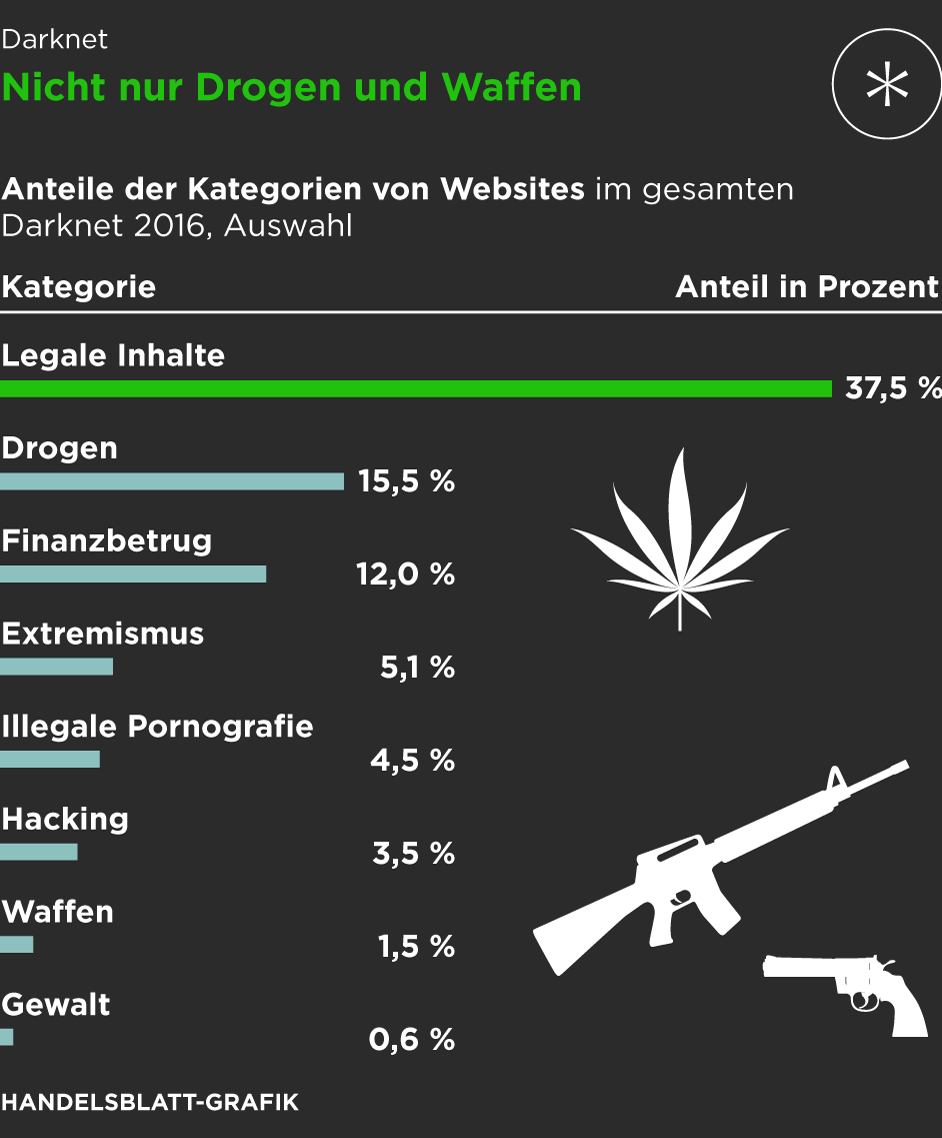
To this end, we report the top 25 users, their member title, and their current and future sales for September 2014 for these measures in Table 2. Darknet markets have emerged as a significant component of the digital underworld, enabling anonymous transactions for illicit goods and services. This paper examines the structure, operations, and impacts of darknet markets, exploring their role in global cybercrime. It also analyses law enforcement responses and the evolving security mechanisms employed by these marketplaces. The paper concludes with a discussion on potential regulatory frameworks and the future of darknet markets. The advent of the internet revolutionized commerce, but it also facilitated underground markets that operate outside legal oversight.
- First, in the USA, it is a federal offense to use the USPS for any of these transactions.
- If you ignore the markets that only allow for the sale of illicit drugs, there are still 32 darknet markets currently operating!
- Interestingly, considering users with higher betweenness centrality in the communication network further improves performance, also identifying successful vendors with moderate activity on the forum.
- Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones.
- To ensure transaction security and protect buyer information, sellers on darknet markets use encryption techniques and anonymous communication tools.
- Like ransomware, criminals can buy software and inject your devices with viruses.
The Darknet In 2024: Key Trends And Projections
This statement (canary) is usually displayed on a page in the market and is signed with the operator’s Pretty Good Privacy (PGP) signature. The statement has the date of the next update and proof of the date the current statement was signed (e.g., this could be the latest Bitcoin block hash). Users will be aware that operators may have lost control of the market if the canary is not updated within the mentioned date.
Cybersecurity Workforce Trends In 2025 – Skills Gap, Diversity And SOC Readiness
As we look towards the future, it’s crucial to stay one step ahead of evolving trends. With global efforts and initiatives in place, we can combat these dark corners of the internet and ensure a safer society for all. It’s crucial to stay informed about these risks and adhere to proper protocols to protect yourself and others from falling victim to these illicit activities. By being vigilant and advocating for stronger healthcare regulations and public safety measures, we can create a safer environment for everyone involved. One major issue is the illegal sale of prescription drugs on these platforms, which not only bypasses regulatory controls but also puts individuals at risk of consuming counterfeit or substandard medications. You’ll examine how these illicit online platforms facilitate the movement of illegal funds and contribute to the proliferation of financial crimes.
Response Time
Thus, betweenness centrality is able to detect the largest share of successful vendors not included by any of the activity indicators. Therefore, reducing the set of users for law enforcement to investigate using betweenness centrality may provide a fresh perspective. In this paper, we investigate to what level employing network measures computed on user-to-user communication networks are useful in identifying both current and future successful vendors on cryptomarkets. We look at three law enforcement applications, each increasingly more useful to law enforcement practitioners. Furthermore, we study the Evolution cryptomarket at different points in time, i.e., we look at at various snapshots of the communication network. Consequently, we propose a methodology with the potential to serve as an early warning signal for future vendor success on cryptomarkets.
Malware Sales
The market operators have graded the importance of different bugs, including info, low, medium, high, and critical. In terms of scope, this program covers various types of vulnerabilities, such as UI issues, server-side disclosure, sensitive data disclosure, authentication bypass, command execution, etc. These are all old and now trivial approaches that the CAPTCHA community has abandoned years ago.
What Are Some Common Ways That Individuals Access Darknet Markets?
At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. Significant technological innovations and trends have reshaped dark-web marketplaces over recent years. In 2025, many platforms have adopted decentralized architectures, reducing single points of failure that previously made them vulnerable to law enforcement takedowns.
If someone has the market’s code to the infrastructure, no matter how much effort law enforcement puts in, it will keep coming back on another server or can be built again with the same branding. According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024).
Financial Markets, Financial Institutions, And Fiscal Service

The darknet, the hidden part of the internet that can only be accessed by a special browser, has long been home to various criminal marketplaces and forums. Organizations can adopt AI-powered cybersecurity platforms, integrate threat intelligence tools, and partner with cybersecurity firms for enhanced protection. Using AI to monitor darknet marketplaces involves scanning a large volume of data, which raises privacy concerns.
This way, you can catch any leaks and stop them before they cause bigger problems. Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities. The victims, who are common users, businesses, and even banks, who end up paying the price. If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals.
LATEST POSTS

Moreover, it’s not only the entertainment industry that gets hit; some sell cracked versions of the most expensive software, and others offer pirated eBooks and academic material at cheap prices. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired.
Money Laundering And Financial Crimes
In other words, where degree was a measure of how well someone is connected locally, closeness is a measure of how well connected a node is globally, i.e., to the entire network. RaaS seems to be a small market within the darknet, and vendors are quite resilient in the face of numerous takedowns. Finally, regarding the RaaS target market, the authors found that, based on the items description, most of the RaaS available were targeted to experts while a little bit more than a third were accessible to novices. Moreover, popular items tended to include links to detailed guides and tutorial videos with step-by-step instructions.
This observation once more highlights the potential of betweenness centrality as an early warning signal. Next, we investigate whether these measures can also distinguish between vendors’ levels of success. To assess this, we looked at the relative difference scores between the top percentile and all vendors (Fig. 2a, b) and between the top and sub-top percentile (Fig. 2c, d) for both current and future success. Figure 2a shows that for all measures the currently most successful vendors have on average higher network centralities and activity indicators. After the first month and with the exception of July and August 2014 for betweenness centrality, Fig. 2c demonstrates this also holds when comparing the top with the sub-top percentile.