Always exercise extreme caution when using publicly posted onion URLs. If you can’t get a personal recommendation from someone you trust, verify the URL from multiple sources. If you want to use Tor privately, you can use either a VPN or Tor Bridges (Tor nodes that are not publicly indexed). Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. The dark web, or dark net, is a small part of the deep web that is kept hidden on purpose.

Tools Needed For Safe Access

Onion sites are far safer to use as they are hidden deep within the deep web. Also, since users can only access them using the Tor browser (with its high-end encryption), users can be rest assured their identities and locations remain hidden. Despite crackdowns, the black market continues to evolve, with new platforms and methods emerging regularly.
That push led to the arrest of Ross Ulbricht, the founder of Silk Road, after a long and intense investigation. On the dark web, even a minor slip-up can cause you big consequences. So, you need to be extremely cautious because the fake sites are often very similar to the real ones, making them dangerously convincing.
Keep Your Identity Hidden
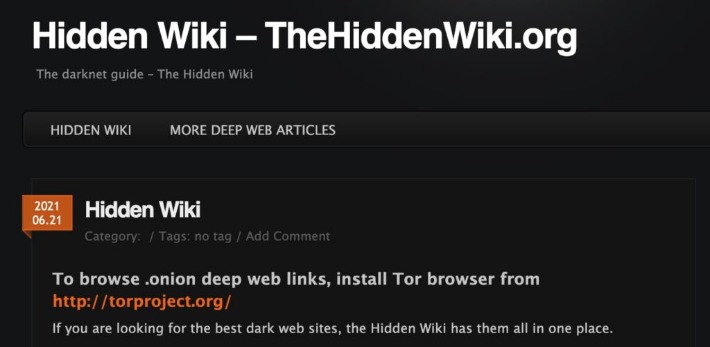
These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information.
Biggest Dark Web Marketplaces
Antivirus will ensure that any viruses or malware downloaded from the dark web are removed. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria.
Tips To Stay Safe When Using The Dark Web
Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. The dark web, or the darknet, is a small subset of the deep web.
- Like other marketplaces, it also requires registration for new users and accepts payments in Monero.
- If you access illegal content or participate in criminal transactions, you face legal consequences.
- You are not required to provide your personal information to create an account.
- These include VPNs, proxy servers, and anonymizing networks such as Tor, which are used to hide a user’s online activity and location.
- One of the earliest and most well-known dark web marketplaces was the Silk Road, launched in 2011 by Ross Ulbricht.
Using Brave Browser (with Tor)
Haystak is often considered one of the deepest search engines for the dark web because it indexes around 1.5 billion dark web pages. While no search engine can cover the entire dark web due to its decentralized and ever-changing nature, Haystak is a top choice for exploring its hidden content. TorlanD opens up access to a vast range of hidden content, allowing you to navigate the deep web freely without restrictions.
Roundup – Best VPNs For Speed
Data like this can also help estimate how many people actively access the dark web and how many hidden websites truly exist—you can even tell where the users are accessing from. With rising curiosity around hidden corners of the internet, many professionals wonder, “how to access the dark web” safely. From cybersecurity researchers to IT managers, understanding how to navigate the dark web can help monitor cyber threats, protect sensitive data, and investigate cybersecurity incidents. Online platforms allowed sellers to reach a global audience, significantly expanding the potential market for their goods and services. The dark web is a small segment of the deep web, which encompasses all parts of the internet not indexed by standard search engines like Google.
Why Are All The Darknet Markets Down
The dark web, by contrast, is configured on darknets — online networks that can be accessed only with special software and techniques. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. If you’re interested in marketplaces, start by learning about the top darknet markets.

Subsequently, we (IV) compare dark web counterfeit prices with prices of the same products on the surface web to understand possible profit margins for the various product types identified. However, it’s worth noting that markets specializing in other illicit goods also bring in sizable funds. We’ll examine card shop activity in greater detail later in this section. Credentials of many online services which include banking, telco, social media networks and many more are being listen in the darknet markets. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods.
That is important for those who may fear persecution for their actions or live in areas where access to information is regulated. E.g. you may wish to get your own hacked account back, or hack into a crypto wallet which stole your funds. You may buy an antique piece which the seller may not wish to publicize on the clearnet and so on. Do note that these lists are completely controlled by the admin, hence, there’s a greater chance of you finding scam links here.
However, when you wish to use the darknet markets, you need iron-clad security. Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web. It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites.