
By gaining an understanding of how the black market for identity data works and steps businesses can take to reduce the chances, can prevent consumers from becoming a victim. Darknet markets still play a role in the cybercrime economy, but their future remains uncertain. Law enforcement efforts are increasingly effective, and technological shifts are changing the way these platforms operate. Use this information responsibly and legally—for research, reporting, or educational purposes—not for participation. Stay safe, stay private, and stay on the right side of the law.
This is made easy, because the anonymity works both ways. You can never be sure who’s really behind the other end of the line. In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains.

What Are Fake IDs And Documents On The Dark Web?
Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic. The core principle of the Tor network was first developed by U.S. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.
- It allows access to the .onion sites on the dark web that you won’t find using a regular browser.
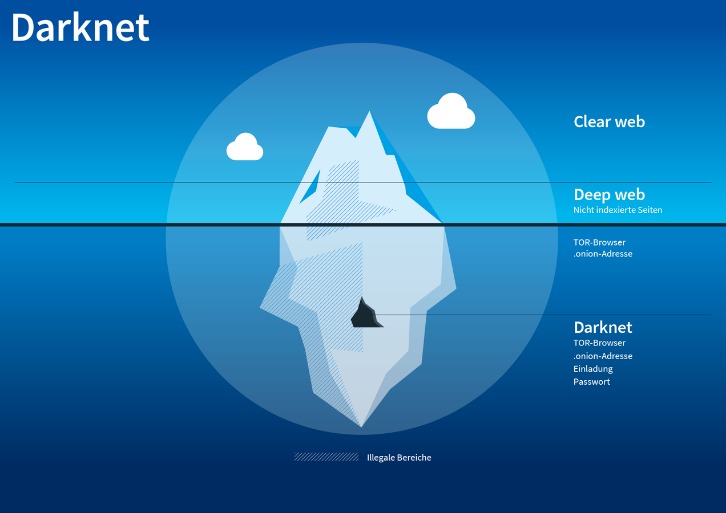
- Darknet markets are websites which are hosted on the deep-web and can be accessed typically using the Tor network.
- When you invest in our IDs, you’re getting more than a product; you’re getting a card crafted to perfection, made to last, and designed to give you total confidence every time.
- And like many legitimate sites, user reviews can make or break a seller’s reputation.
- The payoff values in the scenario of using a fake ID illustrate the dynamics of rational decision-making under peer pressure.
Criminal Hacking Services
- Our authentic designs pay meticulous attention to every detail—state-specific holograms, UV-reactive ink, scannable barcodes, and razor-sharp microprinting.
- It’s not as massive as Abacus, but quality’s on point—vendors deliver, and the community’s buzzing on Dread about it.
- Surprisingly, most guns on the darknet actually start as legal products.
- Recent examples include Yellow Brick Market (exit-scam January 2021) and BigBlue Market (April 2021).
- Registered users can enable PGP-based 2FA, and all communications are encrypted.
The process is structured similarly across most dark-web marketplaces and generally includes using privacy-focused cryptocurrencies, anonymous communications, and secure delivery methods. Fake documents, such as IDs, passports, and driver’s licenses, typically make their way onto the dark web through a combination of sophisticated cybercrime, insider threats, and specialized forgery operations. The dark web—accessible only through encrypted networks like Tor—acts as a shielded marketplace where anonymity protects both sellers and buyers, enabling the illicit trade to flourish largely unseen by authorities.
MoneyWave
FraudFighter™ ID (formerly PALIDIN) offers a robust suite of tools built specifically to meet today’s evolving fraud threats. Some of the offshore forgery vendors are extremely good at what they do. We’ve bought dozens of documents from sites such as Abacus, BriansMarket and Torzon. At this year’s International Association of Financial Crimes Investigators (IAFCI) show, we had the chance to put them in front of quite a few Secret Service, FBI, Postal Inspector and police officers.
The 17 Best Dark Web Marketplaces In 2025

Very detailed vendor profiles show us a vendors total sales, disputes, vending age and other crucial information. It has a large number of listings under Drugs and Online Business categories. It also supports multisig transactions which further increases security.
Popular Links
During our tests for the research, we were able to register with a bogus email and a random username. The market doesn’t verify email and has good security in place. All that one can expect from a deep web marketplace when it comes to anonymity and security.
With our extensive experience, you can feel confident knowing your fake ID is in the hands of skilled experts who value quality above all else. We’re not amateurs—we’re seasoned pros who guarantee results every time. We believe quality starts with the foundation—that’s why we use only premium materials to create our IDs.
The Evolution Of Dark Web Marketplaces
Furthermore, China, Singapore, Turkey, Canada, Israel, and Australia all had averages of either $14 or $15. Incognito’s got a slick vibe—easy to roam, packed with oddball stuff like hacked accounts. Takes Bitcoin or Monero, and last week I snagged a deal that shipped in three days flat. Archetyp’s all about the drug game—ships worldwide, keeps fees low (1-4%).
Dark Web Escrow Links
Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. After the cyberattack on the Bernese IT company Xplain in May 2024, stolen data was published on the darknet. An analysis by the Federal Office for Cybersecurity (BACS) revealed that around 65,000 of the 1.3 million data records published were relevant to the Federal Administration. Around 9,000 of these documents could be attributed to the Federal Administration, with around 14 percent containing sensitive content such as personal data, technical information, classified data and passwords.
Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025
They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024). Like ransomware, criminals can buy software and inject your devices with viruses.
Exploitation Of Anonymity For Harm
Yes, with the right identity verification tools that include biometric checks, document verification, and real-time data matching across trusted sources. Protecting yourself and your organization from fake document fraud begins with proactive measures aimed at safeguarding personal data and strengthening overall security practices. While complete protection may not always be possible, consistently applying strong preventive steps can significantly reduce vulnerability to identity fraud and misuse. Understanding the process involved in obtaining fake IDs and documents highlights both the complexity and the significant risks involved. Despite the apparent ease, purchasers are continuously exposed to potential scams, fraud, interception by law enforcement, and severe legal consequences. Experian’s free credit monitoring service is one easy way to stay alert.
It offers outstanding privacy features and there is currently a discounted rate available through this link. As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down.



