
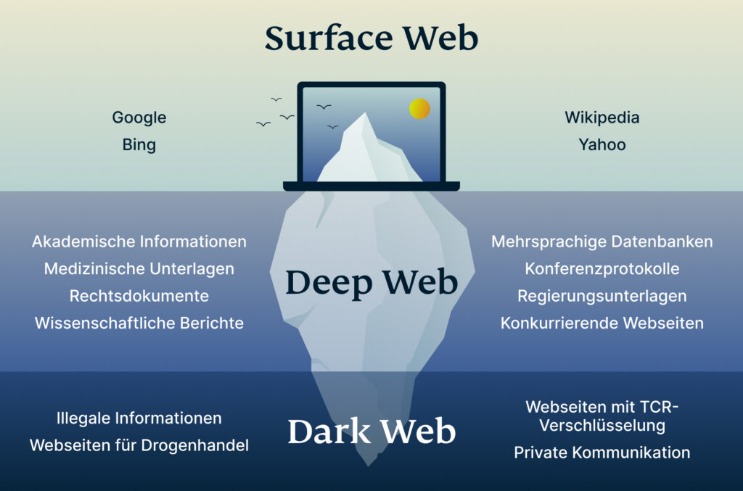
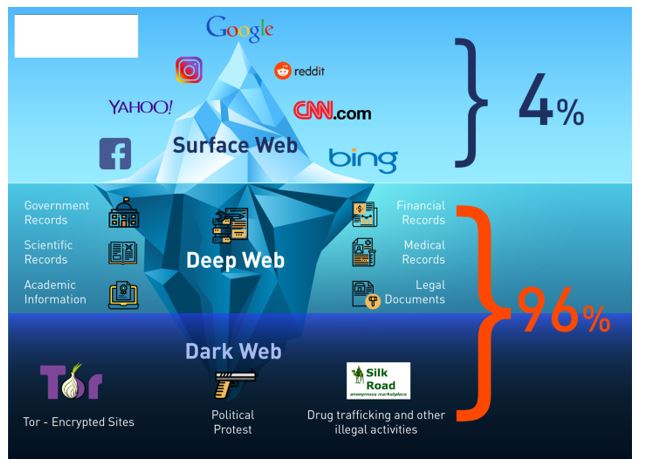
Other sites explicitly block search engines from identifying them. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content. It works by sending internet traffic through volunteer-operated nodes all over the world.
- Law enforcers can use custom software to infiltrate the dark web and analyze activities.
- The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
- For example, it maintains your privacy and enables you to access untraceable content and services.
- As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
- Are Wi-Fi hosts and owners able to see what you’re doing online?
Tor-Browser: Dein Zugangspunkt Zum Dark Web
However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live.
Wer Ist Der Eigentümer Von Tor?
This means your activities cannot be traced or your browser history exposed. The early version of Tor was created to mask spy communications. In due course, the framework was remodeled and made public as a secure browser. Everything you find on the dark web is not necessarily illegal. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web.
Best Tor Sites Available On The Dark Web – Quick List
Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal. The use of the dark web raises suspicion as it shows there is something you want to do privately. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Think of Tor as a regular browser like Firefox, Google, or Safari. The only difference is that it passes your traffic through random nodes before reaching the destination.
Brauche Ich Ein VPN, Wenn Ich Tor Verwende?
The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution.
Was Ist WPA2 (Wi-Fi Protected Access ?
It is a relatively new provider but offers better features than most established VPNs. ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage.
These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. This .onion site is a bit different from the others reviewed above. The Imperial Library is a dark website with many digital books.
- One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online.
- Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
- In most cases, whistleblowers have sensitive information about the government or a company.
- Accessing blocked content can result in being placed on a watch list or imprisonment.
- Also, you can set a strong password to protect your message and choose how long it will take to expire.
Use A Secondary Non-admin Account
Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. No user names are tied to actual identities, and no moderation like one may find on Reddit.
With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. The biggest and most frustrating part about dark websites is that they live for a short span of time.
Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity.
For safer browsing, it is highly recommended to also use a VPN and antivirus software. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article). Though people usually think of dark websites as the wrong online place, that’s not the complete truth. Although the underground internet world is rife with everything bad, it also hosts positive elements.

Stay ahead of threats and ensure your online safety with our regularly updated content. Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc.

You can also use it within the dark web, as it has .onion links. It will offer you an additional layer of encryption to access the deep parts of the internet. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites.



