
The Hidden Wiki simplifies this by consolidating diverse resources in a single directory. Tor is the most popular instance of a darknet,19 and it is often mistakenly thought to be the only online tool that facilitates access to darknets. Tails (The Amnesic Incognito Live System) is a Linux‑based operating system that boots from a USB stick and routes all traffic through Tor.

List Of Tor Onion Services
You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile.
What Are The Best Onion Sites?
If you wish to access the snapshots of these websites, just type in the domain name, and you will get the results depending on how many records exist on the website. This is a great resource for users looking to refer to old prices or job listings that have changed or are outdated. However, not all books on this site are legally available, so they don’t have copyrights. That means you may violate copyright laws while downloading books, so use a VPN to protect yourself from any legal repercussions if you have a dire need to use it. You can access thousands of issues, from the most popular to the most niche.
RiseUp — A Secure Email And Chat Platform For Activists
- However, because edits are not always verified, malicious actors often insert scam sites, phishing links, or fake marketplaces to steal credentials or cryptocurrencies.
- If you stumble upon any websites that seem illegal, just close the window.
- Though not specifically a .onion service, Keybase integrates well with privacy-focused ecosystems like Tor.
- For veterans, it remains a quick reference for new marketplaces, tools, or resources.
- Many pages have poor encryption standards and no other protections, so simply visiting a Tor site can infect your device.
- However, transactions involving controlled substances or hacking tools trigger the Controlled Substances Act, the Computer Fraud and Abuse Act and the Money Laundering Control Act.
Unlike regular e-commerce sites, markets on the dark web often deal with illegal or highly restricted goods and services, such as fake documents, hard drugs, and hacking services. Sure, you might come across listings for legit products like handcrafted jewelry or digital art, but those are few and far between. Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries.
Bitcoin – New Links (
RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user. A 2014 study found that the most common type of content found on Tor, the most popular darknet, was child sexual abuse material.
A Dark Web Search Engine
In this section, we have listed the most popular resources on the Dark Web. Please note that you must take great care when using the Dark Web as sites often contain adware, spyware, malicious links, and scams. Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. Many mainstream media organizations monitor whistleblower sites looking for news. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer.
There are several whistleblower sites, including a dark web version of Wikileaks. Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. While the Tor Browser provides strong anonymity, using a VPN (Virtual Private Network) alongside it adds an extra layer of security and privacy. A VPN encrypts your internet traffic before it enters the Tor network, hiding your Tor usage from your internet service provider and shielding your IP address from the first Tor relay. This setup can help prevent network-level surveillance and reduce risks in environments where Tor use might be flagged or restricted. Choose a trustworthy VPN service that has a strict no-logs policy and supports connection without DNS leaks.
Email Providers

But while anonymous email services can help protect your identity, they don’t make you immune to threats like email spoofing or social engineering. And it’s still essential to use strong passwords and two-factor authentication (2FA) to help keep your account secure. Standard search engines index these websites and are accessible without special configuration. In an era defined by digital connectivity, protecting sensitive, critical and personal information from cyber threats – including those originating from the dark web – is a strategic imperative.
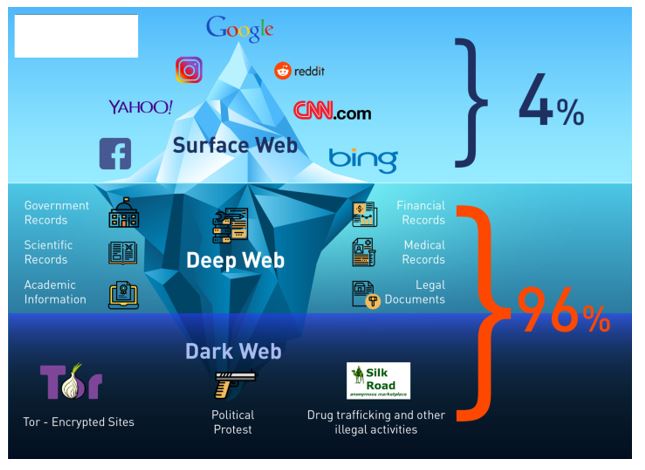
Introduction: How Much Of The Internet Can You See?
Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy. This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement. The use of digital signatures can also help verify the authenticity of users and transactions.
The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit activity compared to the usual internet, which is more vulnerable and trackable. The dark web itself is not illegal, but it’s largely connected with unscrupulous and illegal operations. It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data.
Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed.
Knowing this, we tested many dark websites, and only the safest and most reliable ones made it to our list of 29 best dark web sites you should know in 2025. As a result, your dark web use may draw unwanted scrutiny from your ISP or law enforcement. Using a VPN can help strengthen your privacy while visiting the dark web. While many dark web websites, like the former black market website Silk Road, are used to facilitate criminal activity, there are also plenty of legitimate dark web websites. mark it means it has been verified as a scam service and it should be avoided.|Above all, keep your Tor Browser and security software updated, and use privacy-focused browser settings to minimize exposure. The Hidden Wiki is accessible primarily through specialized anonymity networks like Tor and, to some extent, I2P (Invisible Internet Project). These tools enable users to connect to .onion or .i2p sites that exist outside the conventional internet infrastructure. Tor, the most widely used, anonymizes traffic through layered encryption and random routing, providing a secure way to access dark web directories safely.}
Is Using Tor Safe?
That’s why many people choose to do so anonymously on the dark web, rather than using the clear web version of the site. The dark web is home to a variety of useful and legitimate resources — educational materials, encrypted email services, anonymous forums — that can’t be found elsewhere. Safe browsing on the Hidden Wiki requires a combination of technical precautions and behavioral discipline. Always access the Hidden Wiki through the official Tor Browser, never via a standard browser.



