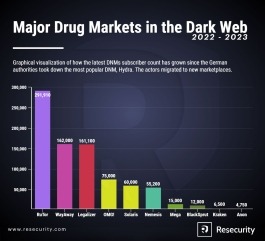
The rise of verified market lists has further simplified access to these platforms, ensuring users can connect to legitimate and secure marketplaces without the risk of phishing or scams. Additionally, the growing popularity of darknet forums and magazines has created a robust ecosystem where users can share reviews, discuss trends, and stay updated on new market links. In conclusion, this paper presents the outcome of our investigation into how security mechanisms are implemented in mainstream dark web markets. In particular, we highlight that the twelve dark web markets we observed have different levels of security to protect themselves and their users. At this stage, we believe that using manual labour in data collection on the dark web market is unavoidable though we would not be surprised if soon enough this can be automated.
If you’re curious about what’s going on in the dark web next year, you’re in the right place. I’ve been digging into marketplaces like Abacus and AlphaBay for a while now, and this page breaks down what’s hot in 2025. You’ll find reviews, quick tables with the nitty-gritty details, and some practical tips on using Monero (see how) or setting up PGP (check it out). Plus, we’ve got some fresh takes on dark web trends and how to get started. This market specialized in selling marijuana related products and magic mushrooms, with no “hard drugs” for sale. DNMs have a limited life and may be shutdown suddenly, leaving users with unfulfilled orders and sellers with no means of communication.
Here, we set out to find the main actors in the DWM ecosystem and assess their systemic impact on a dataset of 40 million Bitcoin transactions involving the 31 major markets in the period 2011–2021. Importantly, the algorithm returns reasonable estimates for the number of sellers when compared against a benchmark of nine DWMs where estimates exist. Then, we reveal a concentration of activity around an elite group of participants, where a large fraction of the trading volume is driven by a small number of players. We find that trading properties of buyers and sellers reflect the dominance of DWMs in the ecosystem. In particular, we analyse networks of ‘multihomers’, defined as users that are simultaneously trading in multiple markets.
Accessing Darknets
Even though DuckDuckGo is the Tor browser’s default search engine, it doesn’t index dark web websites, which means you won’t be able to find .onion sites with it. It is a useful tool for people who value their privacy and want to protect their communications with default end-to-end encryption, zero-access architecture, and minimal personal information requirements. Unfortunately, many dark web websites are devoted to the illegal trade of leaked personal information. If you’ve ever experienced an uptick in phishing attacks and spam after a data leak or breach, it may be because your personal information has been posted to the dark web. Darknet markets trace their origins to the early 2000s, with the advent of Tor in 2002 by the U.S.
The Birth And Rise Of The Silk Road
Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data. However, these platforms often faced law enforcement takedowns, technical issues, or exit scams, where operators vanished with user funds. The continued growth of dark web markets creates urgent concerns for cybersecurity professionals. Stolen data remains a top-selling commodity, with new breaches appearing almost daily. Hackers bundle login credentials, credit card details, and identity documents for sale in bulk.
Vendor Shops Replacing Big Markets
If you purchase something from such shops and make payment through conventional payment methods like your bank transfer, credit/debit card, or PayPal, you can be caught easily and face legal consequences. The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience. Like other marketplaces, ASAP Market also requires you to register for an account. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins. If any user is found not complying with the law, strict and immediate action will be taken against them.
Abacus Upgrades
The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records.

Top Dark Web Markets List: History, Evolution, And Current Landscape (
Some use them due to privacy concerns, such as journalists talking to informants or whistleblowers, while others may simply want to protect their confidential information from observation or tracking. Nevertheless, most people on the internet do not need to communicate or venture into the dark web. The dark web is a hidden section of the internet that you cannot reach with common search engines like Bing or Google. The only way in is through the use of special software that renders all users anonymous and untraceable.
Europol-coordinated Global Operation Takes Down Pro-Russian Cybercrime Network
Specifically, to be classified as a multiseller, a user must be classified as a seller in at least two markets simultaneously. The multihomers play a crucial role in the ecosystem because they act as edges between markets. Hence we do not distinguish multisellers by the number of markets in which they operate.
The largest component of the S2S network one year before and one year after the operation Bayonet. Nodes are sellers that are active within the time period, and an edge is placed between two sellers if at least one transaction occurs between them during the period. To study the performance of sellers, we analyse the quarterly median income, i.e., the quarterly median of the money received by each seller, for each category and multisellers, as shown in Fig. We find that multisellers have the largest median income throughout the period of observation—except in the last quarter of 2017 and 2018, when they have the second largest median income.
- See how our intelligent, autonomous cybersecurity platform harnesses the power of data and AI to protect your organization now and into the future.
- The use of encrypted messaging and secure payment methods ensures that transactions remain private and secure, fostering a thriving environment for trade.
- Always use a fake name and a temporary email address when you buy something from the dark net shops.
- When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements.
Secure Tor Access

The stolen data included names, contact information, and order histories. Dark web listings surfaced almost immediately after the breach, advertising this information for sale to cybercriminals. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats. In 2025, alliances between cybercriminal syndicates and state-backed hackers have grown more common. These collaborations increase the scope and impact of attacks, often targeting infrastructure, defense systems, and financial institutions. Rivalries between nation-state actors have also spilled into the dark web, with turf wars emerging between different sponsored groups over control of marketplaces and services.
Brian’s Club has been around since 2014 and remains one of the most well-known credit card shops on the dark web. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data.
In the vertical axis, markets are in the chronological order of their launch date, although for some markets the activity effectively starts after the launch date (e.g., AlphaBay). The structural change in the multiseller network and the resilience of the multibuyer network. Temporal network of multisellers (top) and multibuyers (bottom) between markets for each year. Edges are multihomers, i.e., traders that are simultaneously active in both markets (sellers in the multiseller network, and buyers in the multibuyer network). The width of the edges is proportional to the number of multihomers acting between the markets.