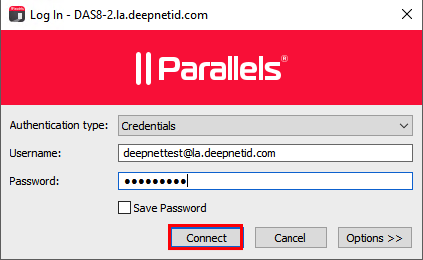
By following simple yet crucial safety measures, you can effectively minimize risks and safely satisfy your curiosity about the hidden parts of the internet. Accessing the deep web is simple, and you likely use it daily when logging into private accounts like Gmail, your bank account, or even streaming services like Netflix or Disney+. To get on the deep web, you must first create an account with the website you want to visit or have profiles with them via other means.
The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites. It lets you search both clearnet and dark web sites, but it blocks all trackers, doesn’t use your location data, and never stores your search history. Now that we’ve learned how to use the best dark web websites to find useful and interesting information, perhaps it’s time to explore other interesting websites. For instance, you may want to tease your brain with one of these intellectual websites serving every category. If you’re having trouble opening a specific onion link, or the overall Tor speed is slow, we have detailed tips on how to make Tor faster.
OnionLinks
- Haystak is a dark web browser that offers better filtering features that help users refine their search results, enabling them to locate exactly what they need.
- With 256-bit AES encryption, this platform enforces its two-fold service of secure messaging and zero logs of your activity.
- For example, to use a banking app, you must have an account with the bank.
- If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic.
- That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy.
These onion websites are specifically designed to be accessed through the Tor network, a free and open-source software for enabling anonymous communication. The “onion” in their name refers to the multiple layers of encryption that protect user identity and activity, much like the layers of an actual onion. However, this same anonymity also makes onion websites a breeding ground for illicit activities. Users often turn to the dark web for private communication, whistleblowing, or accessing restricted information in censored regions.
Market Value And Popularity
Researchers, investors, and enthusiasts rely on Blockchain.com’s data to understand market trends, making informed decisions based on comprehensive blockchain information. Hidden Answers is an anonymous question-and-answer platform located within the dark web, serving as a unique confluence of curiosity, information exchange, and anonymity. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. At TecnetOne, we offer a specialized cyber-patrolling service for businesses, designed to continuously monitor these hidden spaces.
Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa. The good news is that the platform will not see what you copy/paste. Your data is encrypted in the Tor browser before reaching the ZeroBin servers. The Tor Metrics is a good place to get more information about the Tor project.
Dark Web Search: The Best Dark Web Search Engines In 2025
The second category consists of data stores, which specialize in stolen information. For cryptocurrency enthusiasts, Wasabi Wallet is considered an indispensable trading tool and one of the safest ways to buy, sell, and manage cryptocurrency on the dark web. Wasabi Wallet isn’t free to use, but, for a small fee, you get reliable and anonymous cryptocurrency transactions. Many of the newspapers on the site are exclusively on the deep web; they will not show up on Google. Dark web domains are generated in a cryptographically secure way, so they look like random strings of 16 characters or more (like 3g2upl4pq6kufc4m.onion, for example). For example, I looked up google.com and was able to find a snapshot of Google’s home page from 2008.
The Danger Of Tor Network
While accessing the dark web may be perfectly legal in some regions, other places may restrict or scrutinize such activities more heavily. Engaging with certain types of content—such as copyrighted materials, illegal drugs, or illicit services—can lead to serious legal consequences. If you’re unsure about the legal boundaries in your country, consulting a knowledgeable attorney or reviewing reputable sources of legal information is a prudent first step. Topics on Hidden Answers vary widely, encompassing areas such as technology, privacy, politics, and beyond.
Verify All onion Links
There are several programs that hackers frequently use on the dark web. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor.
Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. Many mainstream media organizations monitor whistleblower sites looking for news. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape.
The archived page is then assigned a unique URL, which can be used to access the snapshot at any time, independent of the original web page’s status. This feature is especially useful for preserving evidence of web content that may be legally or historically significant. The Comic Book Library is a digital archive dedicated to the preservation and dissemination of comic books, graphic novels, and related paraphernalia. This repository serves as a comprehensive resource for enthusiasts, scholars, and the general public interested in the rich history and diverse culture of comic books.
Verified Social Channels And News Sites
- Its clean interface and lack of ads make it much easier to use than other dark web search engines.
- It helps people anonymously use the BBC website without restrictions.
- With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity.
- These search engines work best if you already know what site you’re looking for, not for general browsing.
Archive.today is considered an important tool to track changes across government and corporate websites, preserve cultural heritage, and keep knowledge outside of autocrats’ reach. You can archive any site you want, or retrieve historical records wherever available. Radar Rundown Hiding your IP address is one of the best ways to protect your online activities from …
Legitimate Use Cases For The Average User
Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials. It also includes any content that its owners have blocked web crawlers from indexing. There are many legitimate uses for dark web services and communication. The integration of web content into the Surface Web involves the deployment of web crawlers by search engines like Google, Yahoo, and Bing. These digital explorers traverse the vast expanse of the World Wide Web, indexing its content for public access.
However, the threat of clicking on the wrong link always remains, so be cautious while you use it. For individuals in locations facing strict restrictions or those under oppressive governments, ProPublica is the perfect platform to share their stories. ProPublica aims to bring controversial, repressed stories into the open for all to see.
Here’s practical advice for building targeted search queries and safely navigating .onion websites. If you’re curious about how to explore .onion sites safely and effectively, this guide will walk you step-by-step through the process. Let’s start by demystifying how dark web search engines actually work. Yes, police can track users on the dark web, but it’s challenging and resource-intensive, requiring advanced tools, undercover operations, and digital forensics to uncover illegal activity. So, while the dark web is designed for anonymity, it’s not impenetrable — mistakes by users, metadata leaks, compromised devices, or cooperation from hosting providers can all lead to exposure. These illicit items can sell for anywhere from a few bucks to thousands of dollars.
I Found The Easiest Way To Delete Myself From The Internet – And It’s Fast
While many dark marketplaces have been shut down by authorities, new ones soon appear in their place. Social networks, such as Facebook, have created dark web versions of their sites to address privacy problems related to their surface web versions. ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users. You don’t need special tools or a special browser like you need to access the dark web (more about that later). Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information. Dark web links can change frequently, so always verify addresses from multiple trusted sources before visiting any .onion site.