Besides ever increasing hosting costs, the site will have to contend with authorities, attacks from hackers, and...
access
Selecting the optimal tool depends primarily on your individual privacy requirements, technical expertise, and the specific contexts...
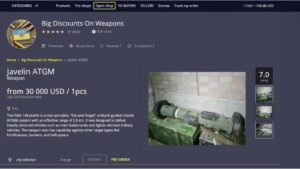
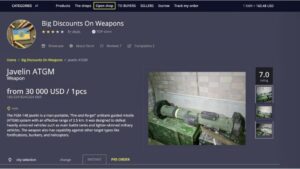
Often viewed as a shadowy underbelly of the internet, it offers goods and services that are not...
It is made up of two virtual machines – a Gateway and a Workstation. All traffic must...
Finally, you need to enter website addresses to access content on the dark web since you can’t...
Therefore, you should use a reliable VPN to hide your identity and create a safe cloud while...
These included back alleys, hidden storefronts, or even in plain sight at flea markets, depending on the...
This makes it even harder for third parties to see your email traffic. Many social media platforms...
First — and this is strongly recommended — you should install a Virtual Private Network (VPN). Also, you...
As mentioned before, your ISP and government institutions are not able to see what sites you visit...