
Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. On one hand, it offers privacy for whistleblowers, journalists, and citizens in oppressive countries. On the other hand, it’s notorious for enabling illegal activity, including drug sales, weapons trafficking, counterfeit ID trading, hacking services, and the exchange of stolen personal data. Some vendors offer services to help people “clean” illegally obtained funds using cryptocurrency and fake transactions.
In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures.
Illicit And Risky Use-Cases
But in addition to the marketplace, darknet participants also need an untraceable payment method in order to maintain maximum confidentiality in their activities. Silk Road was the first darknet marketplace to use the anonymity of cryptocurrencies for payment, thus paving the way for today’s underground world of dark web marketplaces to follow suit. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace.
Escrow Dominance
It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any goods and services. The marketplace is much more organized, which makes it easy to use and navigate. Its intuitive interface and advanced search features make it easy to find local and global products. The marketplace extensively vets vendors listed within its deep web environment that offer a wide range of product portfolios, including security solutions, digital services, and specialized equipment. It stands as a reliable alternative to the defunct Alphabay Market as it continues to position itself as the premier source for advanced privacy-focused digital commerce.
Largest Western Darknet Marketplace Abacus Market Vanishes With Millions In Suspected Exit Scam
Despite a 2019 breach that exposed over 26 million credit cards, it continues to operate, indicating sustained trust in its data pipelines. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. And, of course, think twice before sharing too much personal details online. Even the smallest details about you can be useful to cybercriminals. That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web. But these efforts of law enforcement don’t go in vain; hackers and criminals lose trust if a website or marketplace goes down.
Metaplanet Expands Bitcoin Reserves With 103 BTC Purchase, Nears 19K Total
Darknet chatter on the matter shows that this information has been circulated between malicious actors before the leak that happened in August 2020. Therefore, credentials to affected Japanese organizations’ Pulse Secure servers could be used by different actors in their malicious campaigns, including ransomware attacks. Over the last three months, KELA observed several accesses to Japanese organizations being sold in the darknet. Exposed data may include personal information of companies’ customers and employees, sensitive internal documents, and credentials to the company’s resources. For example, the KelvinSecurityTeam hacking group has been trading a database of a major Japan corporation since July 2020.
Dataset Details

Darknets (i.e. networks on the Darkweb) provide the ideal environment for a wide range of criminal activities. Just as new threats appear on the Clearnet (i.e. the regular Internet), darknets can facilitate similar attacks that provide perpetrators with a greater degree of anonymity. This anonymity makes investigation and prevention more challenging, but still possible. Markets like Perico represent the next wave — safer for vendors, harder for law enforcement to trace, and accessible only to privacy-savvy users. For cybersecurity professionals, journalists, and policymakers, understanding how these systems evolve is crucial to monitoring and mitigating the impact of underground economies.
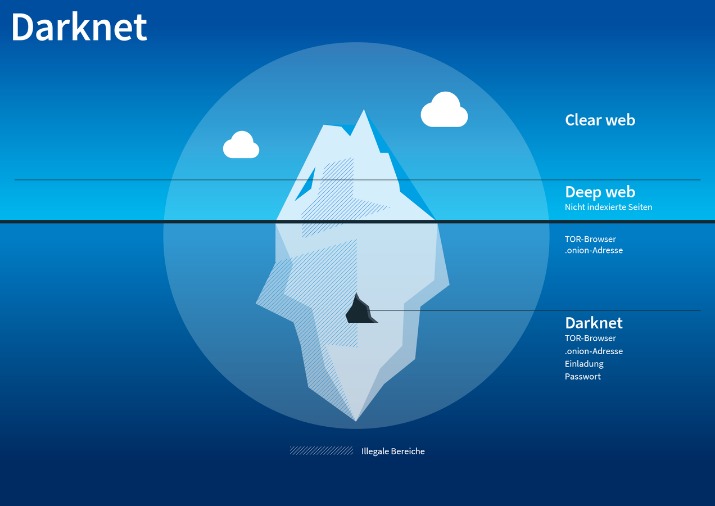
Darknet Marketplaces (DNMs) And How They’re Accessed
Convert and track crypto rates for darknet marketplace transactions—stay ahead of the game. As a user or cybersecurity professional, approaching these marketplaces demands utmost caution, thorough knowledge of operational security, and constant awareness of legal boundaries. Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital environment.
Understanding The Risks

While DNM and fraud shop revenues declined in 2024 following years of concerted international law enforcement efforts, these platforms have managed to sustain their operations by adopting new tactics. A series of law enforcement takedowns in the last few years have shaped the 2024 drug and fraud ecosystems. While 2024 was likely a record year for crypto crime revenue overall, darknet market (DNM) and fraud shop inflows fell, with DNMs receiving just over $2 billion in BTC on-chain, and fraud shops $225 million. Emerging trends shaping darknet marketplaces in 2025—insights into cryptocurrency trading and security. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof.

Collecting Threat Intelligence
Serving 15,000+ users and 1,200+ vendors, it holds an 8% share of darknet drug trading. Known for its robust escrow security and diverse offerings, Abacus is a top choice for 2025. Below are 2025’s leading darknet markets, ranked by listings, trade volume, and vendor reliability. Each offers unique strengths in cryptocurrency trading and escrow security—essential for navigating the onion network.
With 14,000+ users and 1,000+ vendors, it’s a versatile crypto commerce powerhouse. Drughub excels in pharmaceutical dark pool trading with 15,000+ listings and $2M monthly via BTC. Serving 8,000+ users and 600+ vendors, it holds a 10% share of drug commerce—an emerging force since 2023. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware.
- Journalists and activists use it to communicate securely in oppressive regimes.
- I’ve poked around; it’s not overwhelming, just a tight selection that works—think curated over chaotic.
- Once the website is coded, the policies created, the admins ready, and the hosting secured, the site goes live on the TOR network.
- This increases the accessibility and sophistication of cyber threats, with far-reaching consequences for businesses.
The Onion Project, or TOR is the predominant anonymous computer network. It works kind of like a VPN, but instead of routing your traffic through one remote server, it routes it through many random servers across the globe. The Silk Road was the first popular DNM which appeared on the scene in back in 2011. Many other DNMs have sprung up since selling drugs, stolen merchandise, stolen information, and more. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels.
- In 2025, 95% of markets prefer XMR over BTC’s public ledger, with transaction volume up 60% since 2023.
- On the dark web, even a minor slip-up can cause you big consequences.
- For instance, whistleblowers, journalists, and activists may use the dark web to communicate securely and anonymously.
- Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users.
- For 2025, they’re tweaking the mobile site, which I’ve been wanting forever—makes it easier on the go, especially if you’re using Tor on your phone (see how).
- It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.
This will increase national security, international cooperation and confidence building in preventive cyber-diplomacy. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet. This was the initial framework for anonymous communication and file sharing. Later in 2022, the US Naval Research Laboratory built on Freenet’s idea to create a secure and encrypted network for sensitive communications, which was later released to the public as open-source software.



