Your data is encrypted in the Tor browser before reaching the ZeroBin servers. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
DuckDuckGo — Private Search Engine That Can Access The Dark Web
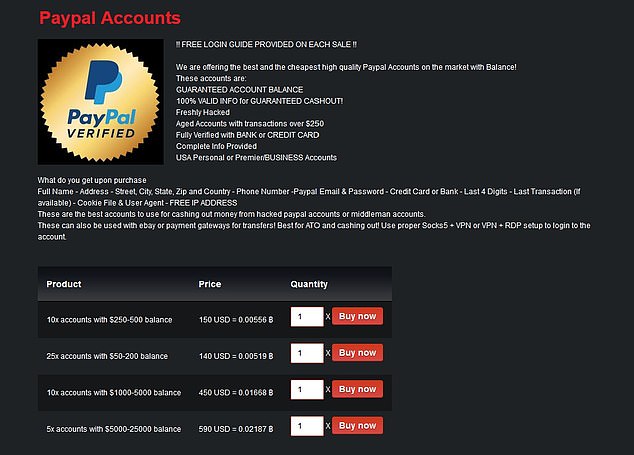
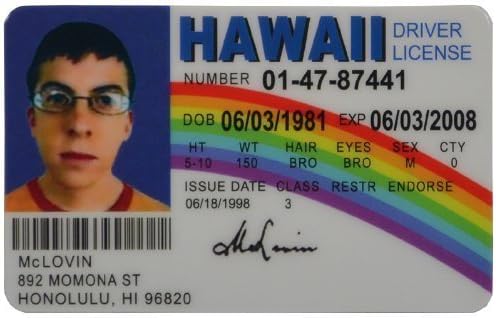
With counterfeiting technology advancing rapidly, fake IDs have gone far beyond crude attempts with mismatched fonts or low-quality materials. Today, they’re more sophisticated and harder to detect, making it critical to understand what constitutes a fake ID and why they’re so dangerous. The data posted on these online illicit shops is a goldmine for threat actors who are looking to commit financial crimes. It provides them with valuable information needed to carry out a variety of attacks.
Encrypted Communication Tools
We quickly ran the ID through our software to see if the barcode generated by CloudPassport would fool any of our barcode security tools. The AI-generated fake ID does not pass our identity verification software. As members of the World Wide Web Consortium (W3C), we uphold the standards for the World Wide Web and work towards a more secure and user-friendly online experience. Identity.com is an open-source ecosystem providing access to on-chain and secure identity verification. Our solutions improve the user experience and reduce onboarding friction through reusable and interoperable Gateway Passes.

Are Sites On The Dark Web Illegal To Use And Visit?
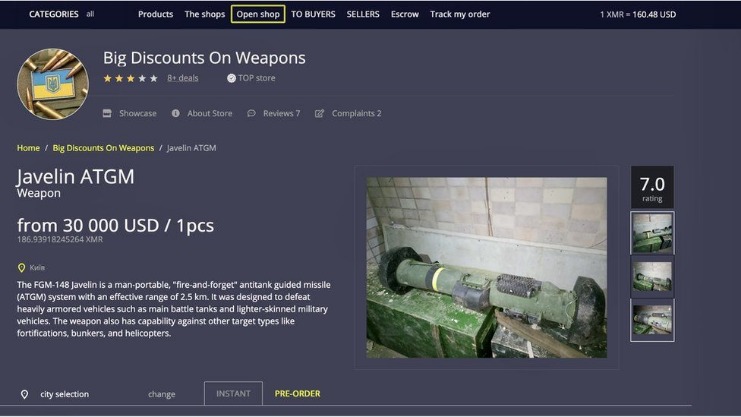
Let’s look at how criminals are using the dark web in 2023 and identify dark web trends so that cybersecurity teams can hone our techniques and defend effectively. To keep your account secure, please avoid using VPNs, VPS, or virtual IP addresses. Miklos founded Privacy Affairs in 2018 to provide cybersecurity and data privacy education to regular audiences by translating tech-heavy and “geeky” topics into easy-to-understand guides and tutorials. While no information is stolen during a DDoS attack, it can be used for extortion or to conceal other hacking activities.
Prices are, however, expected to fall in case of a new cryptocurrency upturn, as this would lead to increased interest and hype from the general public. As a consequence of this, likely fewer crypto trading accounts and wallets were available for hackers to target. The table above shows how much the prices of processing account details have fallen in the last year due to the high supply.
Sales Of Fake Australian IDs Rampant On The Dark Web, Second Only To The US
The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. The dark web has no shortage of criminal activity, scams, phishing sites, suspicious links, and malware designed to trick newbies. And because there’s very little use of HTTPS on the dark net, verifying whether or not a website is genuine using an SSL certificate is not feasible. Dark net websites are called “Tor hidden services”, and they can be distinguished from normal websites by their URLs. Even when using security measures and your common sense, accessing deep web content still poses a risk.

Brief Bio: Real And Rare
A high-quality fake ID should closely resemble a genuine ID in terms of design, security features, and overall appearance. By evaluating these factors, users can select a fake ID website that provides reliable and high-quality fake IDs, minimizing potential risks and legal implications. When deciding on a fake ID website, assessing the available payment options and the platform’s customer care strategy is vital. Many fake ID websites prefer Bitcoin as their payment option due to the enhanced level of anonymity it provides. However, it is important to consider other secure payment methods and ensure that the website offers comprehensive user support. Keybase is an encrypted communication platform that enables secure file-sharing and messaging using public key cryptography.
Robust Digital ID Verification To Catch AI-generated Fake IDs
Despite the undeniable appeal of fake IDs, awareness of possible legal repercussions is necessary. Counterfeit identification documents are prohibited in many jurisdictions, and websites offering such services may face legal consequences. Using fake IDs can lead to criminal prosecution, monetary penalties, and harm to personal and professional standing. Therefore, it is of utmost importance to remain informed and exercise caution when using fake ID websites.

However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live.
Your Go-To For Authentic-Looking Fake IDs By IDGOD
Since the dark web isn’t indexed by standard search engines, sites like Ahmia act as modified directories to help users discover onion sites. You can access onion sites only through the Tor browser or special network configurations. On the Tor network, the onion domain name reflects the fact that, like the layers of an onion, the Tor browser consists of layers of protection. Tor encrypts traffic, masks your IP address, blocks trackers and browser fingerprinting, and doesn’t store a record of your activity.
- While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity.
- This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web.
- The use of such platforms is crucial for maintaining the integrity and security of customer data, and it provides an additional layer of defense against cybercriminal activities.
- It’s made up of forums, marketplaces, and websites you can’t find with a Google search and requires specialized software to access, such as the Tor Browser.
For example, you can only find your Facebook friends, photos, and other information by logging into your Facebook account and finding the information there. On the deep web, you can find such “private” information on web pages. So, that means that the number of pages increased by over 100 trillion in just over three years.
How Do Criminals Use Passport Scans?
Here’s the harsh reality – online payment fraud caused $44 billion in losses in 2024, a figure expected to hit $100 billion by 2029, according to Statista. Fraudsters are constantly finding ways to exploit vulnerabilities, leaving businesses struggling to keep up. Tourist-heavy hubs like Las Vegas, Miami, and New York see the highest concentration of fake ID usage, nearly doubling the national average.
Roundup – Best VPNs For Speed
By understanding and recognizing these state-specific security features, you can more effectively spot fake IDs. People generally buy these accounts due to content restrictions on their own accounts. The hacked accounts may be from country that has a bigger streaming site library than their own. This is kinda weird because people can use a VPN to unblock streaming sites. Here is a profile of a Dark Web vendor, one of nearly 2 million total vendors (active and inactive), who sell stolen, hacked, or bogus data and documents on the Dark Web’s 32 data product sites.



