In 2025, the terms “dark web links” and “dark web sites” have become more familiar to everyday internet users, but the concepts behind them are still widely misunderstood. To grasp what these terms mean, it’s important to distinguish between the surface web, the deep web, and the dark web. From drug trafficking to arms deals to stolen data, the dark web provides a marketplace for many illegal goods and services. This has led to a negative reputation and is attracting the attention of law enforcement agencies. Proton Mail’s dark web version provides end-to-end encrypted email with enhanced privacy protection.
TorLinks – Um Diretório De Backup De Sites onion
Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. They offer user generated reviews of forums and darknet markets, alongside breaking stories and news from the Tor-sphere.
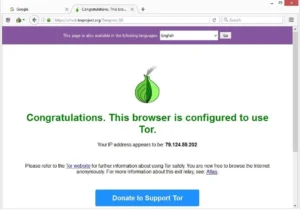
It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web. One of the most straightforward ways to access to dark web safely is via Tor, so we’ve kept that in mind when compiling our list. Your IP is still being revealed to one of the nodes in the onion, meaning your activity and identity can be unmasked. Since academic research is often fenced off behind paywalls, Sci-Hub aims to democratize knowledge by allowing people to see publicly-funded research for free. Facebook joined the dark web way back in 2014, and it remains a viable way to access the website in China and other countries that block it.
Best Free Firewall Software In 2025

Perhaps one of the major attraction factors of these forums is undoubtedly anonymity. Cybercriminals want to carry out their illegal activities without detection by law enforcement agencies and other authorities. Its decentralized community structure makes it one of the best forums, and its security measures help it to withstand threats like DDoS attacks. Ideally, the forum operates within the Tot network, enhancing user anonymity.
What Are The Best Dark Web Websites?
- If you’re concerned a download may be malware, consider running it under Sandboxie or an isolated virtual environment.
- It operates in both French and English and has built a reputation for ease-of-use.
- Since most Tor websites are non-indexed and unregulated, the probability of scams is much greater on the dark web.
- It supports operations in multiple languages and operates on both clearnet and Tor.
Tor encrypts and routes internet traffic through multiple relays, masking the user’s IP address and online activity from trackers and surveillance. This means users can browse sensitive content, communicate securely, or access restricted services without fear of profiling or monitoring. It acts as a centralized hub to access sites that are not indexed by traditional search engines like Google. Many users rely on the Hidden Wiki to find reliable dark web resources safely and efficiently. For users looking to preserve their privacy, knowing how to find real dark web links and access dark web sites that are safe in 2025 is essential.
- Many fake platforms exist purely to steal funds, so only a few services are still active in 2025.
- It organizes links to a wide variety of dark web destinations, including popular marketplaces where users buy and sell goods anonymously.
- Not every visitor is a criminal, but this is where most cybercrimes begin.
- Many exit nodes are actually operated by law enforcement and scammers.
- The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
What Is The Dark Web & How To Stay Safe
Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools. It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in.
Dark web monitoring and threat intelligence firms like Cyble help mitigate these risks with advanced AI-driven threat intelligence solutions. Cyble’s platforms, such as Cyble Vision, monitor the dark web for emerging threats, providing real-time insights to protect organizations from cybercrime. By leveraging such tools, businesses and governments can protect their data and communities from cyber actors. Keybase is a secure platform that lets people chat, share files, and collaborate — kind of like a privacy-first version of cloud storage service Dropbox or communication platform Slack. Everything you send through Keybase is end-to-end encrypted, which means only you and the person you’re talking to can see what’s being shared. Whether you’re sending personal photos, important documents, or just having a conversation, it all stays private and protected from prying eyes.
Is Using Tor Safe?
However, we do not advise readers to log onto this dark web mirror site; doing so would risk their privacy and that of others. With the above dangers, it’s imperative to tread carefully as you step into the dark web. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. Most likely, the native account on your device has full admin permissions by default.

For those, please see the “Fiction Based Subs” section of our sidebar. Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Archive.today collects snapshots of websites and archives them for later viewing. If this sounds similar to The Wayback Machine, the concept is indeed the same. However, The Wayback Machine allows website owners to block their sites from being archived, while archive.today does not.
DeepWeb: Your Expert Resource For Darknet Exploration

After the shutdown of RaidForums, BreachForums filled the gap by hosting discussions on exploits, data leaks, and cybercrime. However, the forum has faced its own set of legal challenges, and its founder was arrested in 2023. Among the most talked-about aspects of these areas are the deep web forums and dark web forums, which serve as gathering places for various online communities. If you need a great Tor VPN, I recommend ExpressVPN — all its servers allow Tor traffic, it has excellent security and privacy features, and it provides fast browsing speeds.
What Is The Deepest Search Engine?
Cryptocurrency tools help maintain privacy and trust during financial transactions on the dark web. The Wasabi Wallet is a Bitcoin wallet that uses CoinJoin mixing to obfuscate transaction trails, enhancing user anonymity. BitBlender provides a mixing service that pools multiple users’ coins to anonymize their origins and destinations. EscrowBay offers escrow services tailored to dark web transactions, holding funds securely until both buyer and seller confirm satisfaction, reducing fraud. Together, these tools facilitate safer, more private financial exchanges essential for dark web commerce. Users turn to the Hidden Wiki because it simplifies navigation through the complex and often confusing dark web.
C The Tor Network
Dark web surveillance involves monitoring information on the darknet, such as to identify compromised credentials being sold, or to track forums to anticipate (and prevent) cyberattacks. While it has legitimate uses, it’s also a hub for cybercriminals, hackers, and other threat actors. The proliferation of IoT and 5G devices will provide new attack vectors for infostealer gangs. As AI becomes more accessible, hackers may use AI-driven tools to automate data theft on a massive scale.
The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. However, most are outdated and have not kept up with the changing landscape.