
ZLibrary hosts free file-sharing access to academic texts, scholarly articles, and general-interest books. It often hosts copyrighted materials without permission, violating many countries’ copyright laws. Downloading or distributing such material is against the law and can have legal consequences.
Keep Tor Browser Updated
It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. Archetyp’s takedown might make headlines, but it won’t stop the trade of illicit drugs on the dark web. It should force us to think about where harm is really happening online and whether current strategies are looking in the wrong direction. In some cases, established sellers on closed-down markets are welcomed onto new markets as digital “refugees” and have joining fees waived. Despite the fact Archetyp had clearly raised the bar on security on the dark web, Operation Deep Sentinel – a collaborative effort between law enforcement agencies in six countries supported by Europol and Eurojust – took down the market.

Protecting Against Malware And Exploits
Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble. By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP.
Onion Links Directory 2025
For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated. The Dark Web and Darknets offer valuable spaces if you value privacy, freedom of speech, or research security technologies.If you misuse them, the consequences can be severe. Like any tool, it can be used for both legitimate and illicit purposes. Unlike the Deep Web, Darknets are intentionally hidden and designed to preserve privacy and anonymity.
Reporting Countries
Terence decided to begin buying online because—as a mid-career professional and father from Minnesota, now in his late 30s—he no longer has the connections that he did when he was formerly addicted to heroin. He wanted to be able to buy high-quality psychedelics from a trusted, reliable source and the dark web seemed like the best place to do so. Marie had never purchased drugs in the conventional way—and still hasn’t.
- Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found.
- One of the most insidious dangers on the dark web is not just technical malware or hidden exploits, but the human element—scammers and con artists who rely on psychological manipulation.
- Open-source intelligence gathered in the aftermath shows how the dark web infrastructure responded and what this reveals about its resilience.
- The Hidden Wiki doesn’t discriminate, so if you randomly start diving into the onion sites listed, you may come across objectionable or dangerous material.
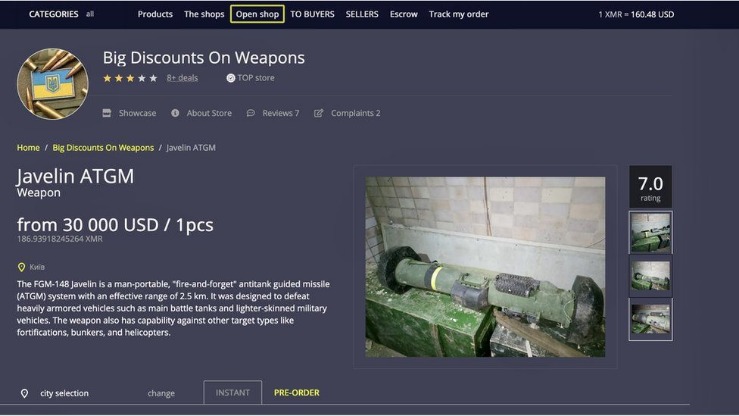
Abacus Market
This digital currency allows buyers to pay while maintaining a degree of privacy protection. Dark web marketplaces are websites where you can exchange illicit goods and services like stolen credit cards, account login credentials, counterfeit items, drugs, and other items. Usually dark web transactions are made with Bitcoin or other cryptocurrencies. Lin was arrested at John F. Kennedy International Airport on May 18 and was presented in Manhattan federal court before U.S. WASHINGTON (SOA) — The dark web is a marketplace of anonymous websites filled with illegal activity, from the sale of identity theft tools to illegal drugs, weapons, and worse.
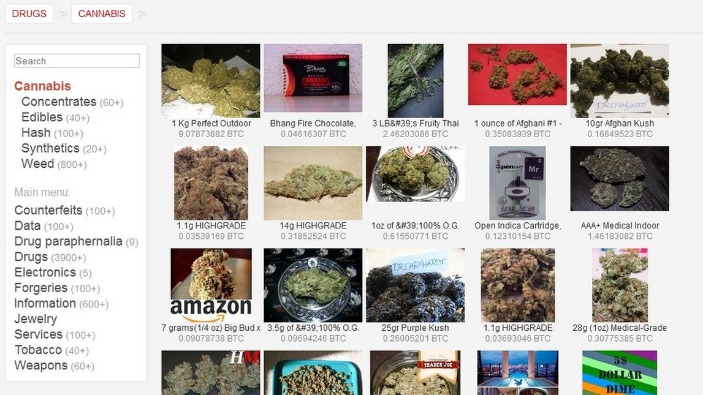
Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. Unlike the traditional drugs marketplace, there isn’t a commonly used template for drug listings published on Telegram. There are dozens of drug-related dark marketplaces with thousands of users (vendors and buyers) that operate on them. Analysis of illegal drugs purchased online revealed that 35% did not match their advertised substances, underscoring the critical need for increased local drug testing services in Australia to mitigate risks and prevent overdoses. What current policing strategies neglect is that dark web markets are not isolated to the storefronts that are the popular target of crackdowns. These are communities stretched across dark and surface web forums which develop shared tutorials and help one another adapt to any new changes.
It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. Code named Deep Sentinel, the operation was the latest in a series of strikes by European authorities against high-volume dark web markets. Led by Germany’s Federal Criminal Police Office (BKA) with support from the Netherlands and the Czech Republic, the operation extended to Spain, Sweden and Romania.
Archetyp Was One Of The Dark Web’s Biggest Drug Markets A Global Sting Has Shut It Down
Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need.
Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download.
Activist And Human Rights Platforms
To facilitate these financial transactions, Incognito Market had its own “bank,” which allowed its users to deposit cryptocurrency on the site into their own accounts. After a narcotics transaction was completed, cryptocurrency from the buyer’s account was transferred to the seller’s account, less the 5% fee that Incognito collected. The bank enabled buyers and sellers to stay anonymous from each other. A lot of illegal activity occurs on the dark web, and onion websites are popular hangouts for cybercriminals and scammers. But if you use antivirus software, avoid clicking shady links, and stick to known sites you should be okay. It’s also a good idea to set up a VPN for an extra layer of protection.
- Neither DuckDuckGo’s dark nor normal versions keep a log of your web activity.
- Drug traders list drug products by using a fixed template, which includes a few sections, including the name and the type of drug, the weight of the product, the location it’s shipped from, shipment details, and pricing.
- The Silk Road on the dark web is often described as one of the most infamous online black markets in history.
- Accessing blocked content can result in being placed on a watch list or imprisonment.
- The keyword in that example is “onioname,” which is right at the start of the .onion link.
E-mail Newsletter
The agency posted video is from a take-down in 2019, called Operation SaboTOR— a play on TOR, the special browser used to access the dark web. “Sometimes not when they’re doing the crime, but when they’re just online doing their own personal thing, sometimes they mix up accounts,” Henderson explained. So, that can run the spectrum—from credit card fraud to sextortion to child exploitation material,” explained Secret Service Supervisory Criminal Investigator Ken Henderson. “You have to be essentially on a list, get invited to the list, to view it at a certain time and place, because obviously it’s the most tracked by law enforcement,” Lott said. The Internet is a vast and complex landscape, much larger than the familiar interface we use every day.



