Because of the level of anonymity, these sites allow cybercriminals, it is critical to use powerful dark web monitoring tools, such as Webz.io’ Lunar, to track emerging financial and reputational threats. With the growing threat from cybercriminals who sell stolen credit card information on the deep web and dark web, businesses need to stay ahead of the game. Over the years several advanced tools have been developed to help track and prevent such fraudulent activities. This is how the site admins encourage users to post their stolen credit card details on their site first. Still, even with these crackdowns and better defenses, dark web markets just keep coming back. As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down.
Cross-Border Regulation & Digital Identity Traceability
- Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity.
- Banks increasingly rely on technologies like machine learning to detect unusual transaction patterns, analyzing large datasets to identify anomalies that indicate fraud.
- It tracks changes to your credit report and helps you spot potential identity theft early, so you’re not the last to know when something goes wrong.
- By consistently applying these straightforward security tips, you can significantly mitigate risks and better protect your privacy, finances, and legal standing when interacting with dark-web marketplaces.
- As mentioned earlier, launching a cyberattack doesn’t require any hacking skills.
The platform’s popularity continues to grow, attracting both new and returning customers. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. In 2024, the platform grew significantly in popularity, partly because of its strategic acquisition of users from a number of recently shut-down marketplaces, such as AlphaBay and Incognito Market, which had recently closed their doors. Two factor authentication (2FA) is now part of NIST and most government standards. 2FA requires that users have access to an email or device where the identity verification request can be sent.
KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Always use a fake name and a temporary email address when you buy something from the dark net shops. You can even use a secure email provider or a burner email address whenever you visit the dark web. A quick guide for developers to automate mergers and acquisitions reports with Python and AI.

Brief Bio: Real And Rare

Many dark web monitoring services are offered as individual solutions in larger platforms and services, so in certain cases, monitoring might not necessarily need to be a specialized choice. Even as the dark web has changed in recent years, several security vendors have introduced new monitoring products that are tied to meet the demand from enterprise users and consumers alike. Then, there is the matter of illegally obtained information from data breaches. Shier said organizations should indeed be concerned about such data being sold or exposed — but not just on the dark web.
Reputable actors active on this forum are often very sophisticated, acquiring a portfolio of positive reviews over the years. Although discussions about ransomware are banned, multiple ransomware-as-a-service (RaaS) operators are still active on the forum to purchase initial accesses or coordinate with partners. The forum is used for all cybercriminal types, but a particularly large population of initial access brokers have been observed, especially in the “Auctions” section of the forum.
Criminal Hacking Services
These software are also capable of launching DDoS attacks and phishing campaigns. These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. Although these marketplaces are continuously shut down by law enforcement agencies, they still work today. Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones.
Topics And Products Sold
Security questions based on data obtained from a third party database can provide another great speedbump to fraudsters who have fullz on a victim. KBA questions are generated based on things like DMV records and utility bills and are designed to be questions that only the true individual knows the answer to. A criminal who has only access to basic information will likely not know past addresses, family member names, or cell phone providers. PatrickStash has two categories, Cards and Cards NoVBV (short for Verified By Visa). The site’s forum representative is very active in advertising the shop, touting automatic refunds, live statistics, and sellers in a range of countries as their USPs. Telegram carding groups have become a significant threat in the cybercriminal community, with tens of thousands of members easily accessible through the chat application.
Operational Security: Staying Anonymous
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. By combining these proactive fraud prevention strategies, organizations fortify their defences against fullz-related fraud and ensure stronger consumer protection. RussianMarket specializes in the sale of “logs”, CVVs, dumps and RDP access. Notably, Abacus explicitly forbids highly dangerous goods, including weapons, explosives, and exploitative material, which has helped maintain a relatively favorable reputation among its user base.
Data Elements Commonly Included
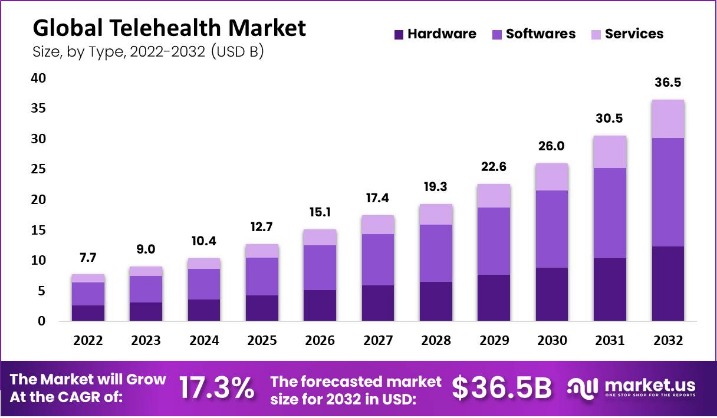
As cyberattacks and data breaches intensify in 2025, the volume of exposed credentials indexed on the dark web has reached unprecedented levels. Identity theft, business email compromise (BEC), and account takeovers (ATO) are now fueled by vast troves of leaked data that are traded or given away for free across dark web forums, Telegram channels, and illicit marketplaces. The exposed data included customer names, addresses, and purchase details.
Fraud Detection Systems
Shortly after the breach, these records appeared on dark web forums, where they were sold to malicious actors aiming to exploit customers through targeted scams and phishing attacks. People have been organizing illicit trades via the Internet since the 1970s. Those early examples, though, were through closed networks, and the actual exchanges of money and goods generally had to take place in person. With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail but easy. As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created.
Protect Against Fullz Fraud
BreachForums, an underground forum that has seen multiple iterations and changes in ownership, continues to be one of the most well-regarded English language forums serving cybercriminals across the world – in spite of a rocky year. The forum is frequented by initial access brokers, database vendors, malware developers, spammers, programmers looking to learn new techniques, and everything in between. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private.
As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria. Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics. When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements. And, of course, think twice before sharing too much personal details online.